Tech Features
ASUS Techsphere Forum: Empowering Business Leaders Through Next-Gen Hardware Innovation

- By: Subrato Basu, Managing Partner, Executive Board &
- Srijith KN, Senior Editor, Integator Media
The line on the opening slide— “Every company will be an AI company”—wasn’t tossed out as a provocation. At the ASUS Techsphere Forum 2025 in Dubai, it landed as an operating instruction. The message across keynotes, the Intel segment, and two candid panels was strikingly consistent: AI stops being theatre the moment you standardize three things—the workspace (where people actually work), the runtime (so models are portable), and the portfolio (so you manage dozens of use cases like a product backlog, not a parade of proofs-of-concept).
A quick reality check on market size so we’re not drinking our own Kool-Aid: the global AI market in 2025 is roughly $300–$400B, depending on scope (software vs. software + services + hardware). Reasonable consensus ranges put 2030 at ~$0.8–$1.6T. In other words, still early—but already too big to treat as a side project.

ASUS: PUT AI ON THE ENDPOINT—AND MAKE IT GOVERNABLE
ASUS’s enterprise stance is disarmingly practical. As Mohit Bector, Commercial Head (UAE & GCC) at ASUS Business, framed it, the fastest way to make AI useful is to put it where the work happens (the endpoint) and to make it governable. Concretely, that means:
- NPUs for on-device inference (privacy, latency, battery life).
- Manageability (fleet policy, remote control, security posture you can actually audit).
- Longevity (multi-year BIOS/driver support) so IT can set an AI-ready baseline and keep it stable.
ASUS thinks about the modern workplace as an Enter → Analyse → Decide loop, this is where the workday actually speeds up—quietly, relentlessly, at the endpoint:
- Enter: the device captures signals—voice, docs, screens, forms, sensors.
- Analyse: retrieval-augmented reasoning + analytics produce options, risks, and rationales.
- Decide: humans choose; agents act—raise tickets, update ERP/CRM—with audit trails.
It isn’t about one blockbuster use case. It’s about standardizing the canvas, so small wins compound every week.

INTEL: FROM SLOGAN TO STACK (AND WHY THE AI PC MATTERS)
Intel’s deck made the “every company will be an AI company” claim implementable. Four slide-level words—Open, Innovative, Efficient, Secure—double as a buyer checklist:
- Open: less cost, no lock-in. The same models should move across CPU/GPU/NPU and PC → Edge → Datacentre/Cloud without rewrites.
- Innovation: treat AI PCs with NPUs, edge systems, and cloud clusters as one continuum.
- Efficient: lead on performance per dollar and per watt; energy and cost are first-class design goals.
- Secure: your data and your models are IP; run locally when you should, govern tightly when you don’t.
A “Power of Intel Inside” platform slide stitched this together:
- AI software & services: OpenVINO as the portability layer to convert/optimize/run models across heterogeneous silicon.
- AI PC: always-on, private inference for day-to-day assistants.
- Edge AI: near-machine intelligence for vision and time-series use cases.
- Datacentre & cloud AI: scale-out training/heavy inference (fraud graphs, multimodal analytics, enterprise RAG).
- AI networking: the fabric that keeps it all moving—securely.
Why the fuss about the AI PC? Because it’s the next enterprise inflection after Windows and Wi-Fi. Slides mapped tangible outcomes:
- Productivity: faster info-find, auto-drafts, note-taking.
- Communication: translation, live captioning, dictation, transcription.
- Collaboration: smart framing, background removal, eye tracking, noise suppression—without pegging the CPU.
- IT operations: endpoint anomaly detection, VDI super-resolution, remote screen/data removal.
- Security: client-side deepfake detection, anti-phishing, ransomware flags.
Under the hood, Intel’s definition is a division of labour: CPU for responsiveness and orchestration, GPU for high-throughput math/creation, NPU for low-power sustained inference—the always-on stuff that makes assistants truly useful. Add vPro + Core Ultra and you get the fleet controls and long-term stability IT actually needs.
One more practical bit I liked: Intel AI Assistant Builder—a portal to stand up local assistants/agents (with RAG) that can run on the PC fleet first, shrinking time-to-value from months to days/weeks and letting you prove the full E-A-D loop before you scale heavier jobs to edge/cloud.
When the “100M AI PCs by 2026” slide hit the screen, heads tilted from curiosity to calculation. The figures—bullish vendor projections (~100M by 2026; ~80% AI-capable by 2028)—invite a haircut, but the signal is unmistakable: endpoint AI is becoming the default.

WHAT THE PANELLISTS REALLY TAUGHT US
RAKEZ (Free Trade Zone)
Posture: Execution-first. Make AI practical on the shop floor and trustworthy in the back office—governed from day one.
What they drive:
- Diagnostics (OEE baselines, defect maps) + data-readiness scans (MES/ERP) so pilots don’t stall.
- Reference lines/sandboxes where vendors prove accuracy, safety, throughput before purchase.
- Template playbooks: CV-QC, predictive maintenance, warehouse vision, invoice extraction/3-way match—each with SOPs, KPIs, integration steps.
- Curated vendors + shared services (labelling, model hosting/monitoring, SOC for AI) to reduce MSME cost/complexity.
MSMEs: “Bookkeeping-in-a-box” to clean ledgers and free cash; pre-negotiated PoC packs (fixed price/timeline, acceptance metrics); compliance starter kit (consent, retention, safety, escalation).
Enterprises: Multi-site rollout playbooks, edge + cloud reference architectures (identity-aware RAG, policy-constrained agents), and assurance artifacts (model cards, change control, audit trails).
Outcome lens: OEE ↑, FPY ↑/DPMO ↓, MTBF ↑/MTTR ↓, faster close cycles, fewer incidents—AI that moves the P&L and passes audit.
Note – FPY — First Pass Yield; OEE — Overall Equipment Effectiveness; DPMO — Defects Per Million Opportunities; MTBF — Mean Time Between Failures (repairable systems); MTTR — Mean Time To Repair
Oracle (Consulting / Applications cloud)
Posture: AI belongs inside the workflows where finance, HR, supply chain, and service teams live. Expect talk tracks like: ground answers in your own records (RAG with policy), instrument before/after outcomes, and treat AI features as part of ERP/HCM/CX—not a sidecar chatbot. The ask from buyers: prove the Enter → Analyse → Decide gains in real workflows (FP&A forecasting lift, supplier risk scoring, HR talent match quality).
Zurich Insurance (BFSI)
Posture: AI as a force for good, scaled with governance. Think hundreds of use cases: claims triage, fraud/anomaly detection, internal knowledge bots—human-in-the-loop where stakes are high, and IoT-style prevention to reward good behaviour. The key is measurement: fewer false positives, shorter cycle times, clearer audit trails—and elevated roles, not replaced ones.
Group-IB (Cyber / Threat Intel)
Posture: AI to defend—and defend against AI. SOC copilots that summarize and enrich alerts, deepfake/phishing detection, behaviour analytics across identities and endpoints, and the emerging discipline of security of AI (prompt-injection defences, LLM gatewaying, data loss controls for AI apps). If you’re rolling out agents, involve your security team early.
Dhruva Consultants (Tax Tech Transformation)
Posture: RegTech + AI to reduce compliance cost and risk. Document AI to normalize invoices/contracts, anomaly detection for mismatches and fraud flags, and a pragmatic “bookkeeping-in-a-box” on-ramp for MSMEs. Non-negotiables: auditability, versioning, segregation of duties for anything that touches filings.
Prime Group (Labs/Certification)
Posture: Risk-scored processes—every lab step tagged with expected outputs, data access, and fallbacks. Near-term wins: smarter scheduling and test selection; long-term horizon: a Mars-ready lab by 2050 aligned with the UAE’s space ambitions. It’s operational excellence today, exploration mindset tomorrow.
Education (Heriot-Watt University, Dubai)
Posture: candid and useful: human-led pedagogy; AI-assisted admin and decision support. HWU brings talent pipelines (AI/Data Science programs), translational research, and applied robotics capacity (think Robotarium-style ecosystems). This is the repeatable talent + research engine enterprises can plug into—capstones, CPD, joint R&D—that shortens the path from idea to pilot.
WHY UAE HAS A STRUCTURAL ADVANTAGE: RAKEZ × HWU
Local context matters. RAKEZ (Ras Al Khaimah Economic Zone) is more than a location; it’s an adoption on-ramp aligned with MoIAT’s Industry 4.0 programs (ITTI/Transform 4.0). Translation: factories—especially MSMEs—get real help to deploy vision-led quality, OEE analytics, and worker-safety use cases, with policy scaffolding and incentives attached.
Pair that with Heriot-Watt University as a talent/research flywheel and you have a short, well-lit path from concept to production: execution zone + skills engine. That’s a genuine regional edge.
SUMMARY
Techsphere’s most important contribution wasn’t a prediction; it was a design pattern. ASUS gives you the enterprise substrate (AI-ready endpoints you can actually govern). Intel gives you the principles and plumbing (OpenVINO portability; CPU/GPU/NPU continuum; PC → Edge → Cloud). The panellists supplied proof patterns across industries. And the UAE context—RAKEZ for execution, HWU for talent/research—shortens the distance from idea to impact.
If “every company will be an AI company,” the winners won’t be the first to demo—they’ll be the first to standardize. Start at the endpoint, insist on portability, manage a portfolio, and make the Enter → Analyse → Decide loop measurable. That’s how the slide turns into the balance sheet.
_________________________________________________________
- Glossary of Technical Acronyms
- OEE — Overall Equipment Effectiveness (measures manufacturing productivity: availability × performance × quality).
- FPY — First Pass Yield (percentage of units passing production without rework).
- DPMO — Defects Per Million Opportunities (defect rate in Six Sigma terms).
- MTBF — Mean Time Between Failures (average time between breakdowns of a repairable system).
- MTTR — Mean Time To Repair (average time to repair a failed component/system).
- AI / IT Terms
- NPU — Neural Processing Unit (specialized chip for AI inference, optimized for low-power sustained workloads).
- CPU — Central Processing Unit (general-purpose processor for orchestration, responsiveness).
- GPU — Graphics Processing Unit (parallel processor for high-throughput math and AI training/inference).
- RAG — Retrieval-Augmented Generation (technique where AI models query external knowledge bases before generating answers).
- ERP — Enterprise Resource Planning (integrated system for core business processes like finance, supply chain, manufacturing).
- MES — Manufacturing Execution System (software for monitoring and controlling production).
- VDI — Virtual Desktop Infrastructure (running desktop environments on centralized servers).
- SOC — Security Operations Center (hub for cybersecurity monitoring and response).
- IP — Intellectual Property (protected data, models, or designs).
- Industry & Enterprise Acronyms
- BFSI — Banking, Financial Services, and Insurance (industry vertical).
- FP&A — Financial Planning & Analysis (finance function for budgeting, forecasting, performance analysis).
- HCM — Human Capital Management (HR technology and processes).
- CX — Customer Experience (customer-facing processes and software).
- ITTI — Industrial Technology Transformation Index (UAE Ministry of Industry and Advanced Technology initiative under Industry 4.0).
The ASUS Techsphere Forum, organized by Integrator Media, brought together C-suite leaders from diverse industry verticals to explore how evolving hardware standards are shaping the future of work. The event highlighted the growing role of AI-enabled PCs, showing how advancements in endpoint hardware can directly support business needs. By balancing industry-specific requirements with insights on hardware innovation, the forum offered executives a clear view of how these technologies can enhance productivity and deliver measurable value across the wider business community.
Tech Features
THE CONVERGENCE OF CRISIS: HOW OVERLAPPING RISKS ARE REDEFINING WORKFORCE MOBILITY IN THE MIDDLE EAST

By Gillan McNay, Security Director Assistance – Middle East, International SOS
In today’s Middle East operating environment, mobility risk no longer arrives in isolation. Organisations are increasingly navigating multiple, overlapping disruptions that converge to affect how, when, and whether their people can move. Geopolitical tension, aviation restrictions, cyber exposure, misinformation, and workforce anxiety are no longer separate risk categories – they interact, amplify one another, and challenge traditional mobility assumptions.
This convergence is redefining what “safe movement” looks like for organisations with employees traveling, deployed, or working abroad across the region.
From Single Events to Layered Disruption
Historically, mobility planning focused on discrete scenarios, weather events, isolated security incidents, or airline strikes. Today, organisations are far more likely to face layered disruption, where one event triggers a cascade of secondary impacts.
A regional security escalation may coincide with airspace closures. Airspace closures may lead to congestion at land borders. Border congestion increases stress for travelers, which in turn heightens reliance on digital communication channels, precisely when misinformation and cyber activity surge. Each layer compounds the next.
International SOS’ Risk Outlook 2026 highlights this shift clearly: risk is now systemic and interdependent, not episodic. For mobility teams, this means plans designed for one‑dimensional threats will be insufficient.
Mobility Is Now a Strategic Exposure
Movement of people has become a strategic risk vector rather than a logistical one. When employees cannot travel as planned, the impact extends beyond delayed meetings or project timelines. It affects:
- Business continuity
- Leadership visibility
- Employee confidence and wellbeing
- Regulatory and duty‑of‑care obligations
In the Middle East, this is especially pronounced due to the region’s role as a global aviation hub and its highly international workforce. When airspace is disrupted in one country, the effects ripple across neighbouring states almost immediately.
As a result, organisations must treat mobility decisions with the same scrutiny as other strategic risks, cybersecurity, financial exposure, or supply‑chain dependency.
The New Reality: Mobility Under Uncertainty
In recent months, we have seen how quickly mobility conditions can change. Routes that were viable in the morning may be restricted by evening. Neighbouring jurisdictions may adjust entry requirements or limit transit with little notice. Information may circulate rapidly on social media before it can be verified.
The most resilient organisations recognise that movement decisions must be conditions‑based, not schedule‑based. Rather than asking “Can we move people today?”, leaders need to ask:
- What conditions would make movement unsafe tomorrow?
- What alternatives exist if a primary route closes?
- Are we prepared to shift from air to land, or to stabilise in place?
This approach requires planning optionality into every mobility decision.
Overlapping Risks Demand Integrated Decision‑Making
The convergence of crisis exposes one of the most common organisational gaps: mobility decisions are often segmented across functions. Security looks at threat levels, HR considers employee impact, travel teams focus on bookings, and IT monitors communications. In a converging‑risk environment, this fragmentation increases risk.
Mobility decisions must be informed by integrated intelligence, security assessments, aviation updates, border conditions, medical considerations and workforce sentiment. When these views are aligned into a single operating picture, organisations can act faster and with greater confidence.
This integrated approach is increasingly reflected in board‑level discussions, as highlighted in the Risk Outlook 2026, where executive oversight of crisis preparedness and workforce risk continues to rise.
The Human Layer Cannot Be Separated From Mobility
Overlapping crises do not only disrupt routes; they disrupt people. Uncertainty around travel amplifies stress, particularly for expatriates with families, employees traveling alone, or teams operating far from home support networks.
From an assistance perspective, we see that anxiety itself becomes a risk multiplier. Tired, stressed travelers are more likely to make poor decisions, rushing to airports prematurely, acting on unverified information, or attempting unsafe routing alternatives.
Mobility strategies must therefore incorporate psychological safety alongside physical safety. Clear guidance, predictable communication, and reassurance that decisions are being reviewed continuously make a material difference to outcomes.
Why “Move” Is Not Always the Right Answer
One of the most important shifts organisations are making is recognising that relocation or evacuation is not always the safest or most effective response. In converging‑risk scenarios, moving people can expose them to new uncertainties if the destination environment changes.
Stability, supported by shelter‑in‑place guidance, supply planning, and continuous monitoring, can be the safest posture while conditions clarify. Mobility planning should define three distinct postures:
- Stay and stabilise
- Relocate to a regional safe haven
- Evacuate out of the region
Each posture requires different triggers, communications, and support mechanisms. Treating them interchangeably increases risk.
Information Discipline Is a Mobility Imperative
Overlapping crises generate noise. For organisations managing mobility, information discipline becomes critical. Decisions based on rumours, unverified social media posts, or outdated aviation updates can lead to unnecessary movement, or unsafe delay.
Effective organisations establish clear information pathways:
- Who validates updates
- Which sources are trusted
- How frequently conditions are reviewed
- When decisions are escalated
This discipline supports faster pivots when conditions change and reduces the emotional load on traveling employees.
Building Adaptive Mobility for the Future
The convergence of crisis in the Middle East is not a temporary phenomenon. Geopolitical volatility, climate stress, digital disruption, and workforce expectations will continue to intersect. Mobility strategies must evolve accordingly.
Resilient organisations are already adapting by:
- Embedding workforce visibility into core systems
- Designing mobility plans with multiple fail‑safe options
- Training leaders to make people‑first decisions under pressure
- Aligning crisis planning with broader enterprise risk management
As the Risk Outlook 2026 underscores, preparedness is no longer about predicting the next event, it’s about building the capacity to adapt when events collide.
A Redefined Measure of Readiness
In this new operating reality, mobility readiness is not measured by the ability to move people quickly, but by the ability to make calm, informed, and proportionate decisions as risks converge.
Organisations that understand this will be better positioned to protect their people, maintain operational stability, and navigate periods of regional tension with confidence rather than urgency. The convergence of crisis is challenging, but with the right structures, discipline, and integration, it is manageable.
Tech Features
SUPPORTING EMPLOYEES ABROAD OR RELOCATING AMID REGIONAL TENSIONS: A STRATEGIC ADVISORY FOR ORGANISATIONS

By Gillan McNay, Security Director Assistance – Middle East, International SOS
Periods of regional tension place organisations under intense pressure to protect their people while sustaining operations. For UAE‑based companies with employees working from abroad, traveling frequently, or facing potential relocation, uncertainty can escalate quickly. Routes change, borders tighten, information moves faster than it can be verified, and employees look to their organisation for clarity and reassurance. In this environment, support must be strategic, deliberate, and people‑first.
Shift From Reaction to Preparedness
The most resilient organisations are those that move beyond reacting to events and instead operate with a preparedness mindset. This starts with acknowledging that uncertainty is not an exception but a condition organisations must continuously manage. Strategy, therefore, should anticipate disruption and define how the organisation will respond before decisions are forced by urgency.
Preparedness does not mean planning for every possible outcome. It means establishing decision frameworks that allow leaders to act confidently as conditions evolve, whether that results in continued remote work, relocation to a safe haven, or shelter‑in‑place with enhanced support.
Establish Workforce Visibility as a Strategic Capability
Supporting employees abroad begins with accurate, real‑time visibility. Leaders must know where their people are, their travel status, and whether they are working remotely, stationed overseas, or in transit with dependents. Visibility should extend beyond employees to include contractors and accompanying family members where duty‑of‑care obligations apply.
This visibility is strategic because it underpins all subsequent decisions. Without it, organisations risk delayed responses, fragmented communication, and uneven support. With it, they can act proportionately, supporting those most exposed while avoiding unnecessary disruption for others.
Differentiate Between Relocation, Evacuation, and Stability
One of the most common strategic mistakes during regional tensions is treating all movement decisions as evacuations. In reality, organisations need three clearly defined postures:
- Stability: Supporting employees to remain where they are with guidance, wellbeing checks, and secure working arrangements.
- Relocation: Moving employees to a safer location, often within the region, as a preventive measure.
- Evacuation: Executing time‑bound movement out of an area due to elevated risk.
Clear definitions allow leaders to choose the least disruptive option that still protects people. Often, relocation or stability with structured support is safer and more sustainable than rapid evacuation.
Prepare Employees Before Movement Is Required
Relocation becomes significantly smoother when employees are prepared before they are asked to move. Strategy should include guidance on documentation readiness, passport validity, visa requirements for neighbouring countries, preferred relocation countries and expectations around timelines and flexibility.
Employees working abroad need to understand not only what may happen, but how decisions will be made. When organisations explain decision triggers, what would prompt relocation, what would not, employees feel informed rather than anxious. This transparency builds trust and reduces panic-driven movement.
Integrate the Human Dimension into Planning
Strategic support must address the human impact of uncertainty. Employees working from abroad or facing relocation are often balancing professional obligations with family concerns, schooling, medical needs, and other emotional strains. Ignoring these factors weakens any relocation or stability strategy.
Effective organisations integrate wellbeing considerations into operational plans. This includes access to medical advice, continuity of prescriptions, support for family travel, and regular wellbeing check‑ins. Leaders should be attuned to signs of fatigue or anxiety and equip managers with guidance to support teams compassionately and consistently.
Communicate With Discipline and Predictability
In uncertain times, communication is as important as movement planning. Strategy should define how, when, and by whom information is shared. Centralised, fact‑based updates delivered at a predictable cadence reduce speculation and rumor.
Employees should know where official updates will come from and which sources to trust. Communications do not need to be frequent to be effective; they need to be consistent, clear, and grounded in verified information. Saying “there is no update yet” is often more reassuring than silence.
Support Employees Who Must Remain Abroad
Not all employees can or should relocate. Many will continue working from abroad in environments affected by regional tension. Supporting these employees strategically means ensuring they have guidance on local conditions, access to support services, and clearly defined expectations around work, availability, and safety.
Stability should be treated as an active posture, not inaction. Regular check‑ins, updated guidance, and contingency planning signal to employees that their situation is being managed deliberately, not overlooked.
Plan for Relocation as a Managed Process
When relocation is required and viable, it should be executed as a controlled, end‑to‑end process. This includes manifesting all individuals, front‑loading documentation checks, coordinating transport and accommodation, and communicating each step of the journey.
Strategically, leaders must also consider what comes after relocation: access to work, schooling for children, healthcare, and communication continuity. Relocation is not just movement; it is a temporary operating model that must be sustainable.
Learn, Adapt, and Strengthen
Each period of disruption provides insight into what worked and what did not. Strategic organisations capture these lessons and feed them back into planning. This may involve refining decision thresholds, improving data accuracy, or strengthening manager training.
Preparedness evolves as operating environments change, and organisations that invest in continuous improvement are better positioned to protect both their people and their business.
A Strategy Built on Trust and Clarity
Ultimately, supporting employees abroad or relocating amid regional tensions is a test of organisational maturity. Clear visibility, disciplined planning, transparent communication, and genuine care form the foundation of resilience. When organisations operate from these principles, employees feel supported rather than vulnerable, and leaders can make decisions with confidence rather than urgency.
Tech Features
IN THE AGE OF AI, THE BEST HEALTHCARE WILL STILL BE HUMAN

By Dr. Craig Cook, CEO, The Brain & Performance Centre, A DP World Company
Healthcare is entering one of the most transformative periods in its history. Artificial intelligence is accelerating diagnostics, enhancing imaging, and enabling more personalised treatment pathways than ever before. These advancements are no longer theoretical, they are already shaping how care is delivered across leading medical systems.
However, as the industry moves forward at pace, there is a risk of focusing too heavily on what technology can do, and not enough on what individuals actually need.
At its core, healthcare is not a technical transaction. It is a human experience. Within that experience, trust, communication and empathy are not optional, they are fundamental.
Strong human interaction between clinicians and clients remains one of the most important factors in delivering safe and effective care. Technology can identify patterns, process data and support decision-making, but it cannot replace the reassurance an individual feels when they are heard, understood and taken seriously. That interaction often determines whether someone follows through with treatment, shares critical information, or seeks support early rather than late.
From a safety perspective, this is critical. Individuals who feel comfortable with their clinician are far more likely to communicate openly about symptoms, concerns and uncertainties. They ask more questions, clarify instructions, and engage more actively in their own care. This level of engagement reduces the likelihood of miscommunication, improves adherence to treatment plans, and ultimately leads to better outcomes.
In contrast, when the human element is diminished, even the most advanced systems can fall short. An individual may receive accurate data but still leave uncertain about what it means. They may hesitate to disclose something important, or disengage entirely. No algorithm can compensate for that gap.
This is why meaningful communication must remain at the centre of healthcare delivery. It is not simply about explaining a diagnosis. It is about creating an environment where individuals feel safe to speak, where their concerns are acknowledged, and where complex information is translated into something clear and actionable.
As artificial intelligence continues to evolve, the role of the clinician will not diminish, it will become more important. Technology should reduce administrative burden, enhance precision, and create time. That time should be reinvested into the client relationship through greater clarity, deeper understanding and more considered care.
At The Brain & Performance Centre, A DP World Company, this balance is central to how we approach care. Advanced technologies play a critical role in our assessments and programmes, but they are always applied within a human-led framework. Every programme is personalised, every interaction is intentional, and every client journey is built on understanding the individual, not just the data.
The future of healthcare will undoubtedly be shaped by innovation. But its success will not be defined by how advanced the technology becomes. It will be defined by whether we use that technology to strengthen, rather than replace, the human connection at the centre of care. Because ultimately, the most powerful tool in healthcare is not artificial intelligence. It is trust.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR12 months ago
VAR12 months agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Tech Interviews2 years ago
Tech Interviews2 years agoNavigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Trending5 months ago
Trending5 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 Tech News9 months ago
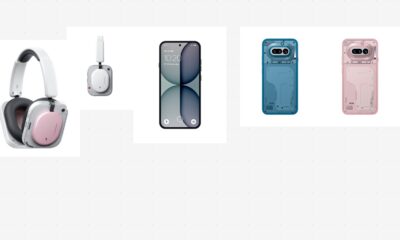
Tech News9 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive1 year ago
Automotive1 year agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms