Tech Interviews
Protecting Each Device is Difficult
Vulnerable urban futurism technologies are not only fair game for mischievous hackers but also crime groups and hostile nation states, warns Steve Hicks, Head of Global Sales, BullGuard in a discussion with VAR.
Q1. Smart homes are central to Internet of Things (IoT) which makes them susceptible to cyber-attacks. How can smart homes also be made safe homes?
A1. It’s difficult to protect each individual device. This places too much onus on the owner if they, for instance, have six or seven smart devices in the home. Even well-known brand devices have proved to be vulnerable to hacks while many mass-produced devices have really poor protection such as default passwords and admin details.
Protecting all devices in a home requires time and technical insights that most people don’t have. These include looking for firmware updates and keeping an eye on network traffic to see if something is leaving or entering the network that shouldn’t. What is required is an overarching protection that starts at the network router, monitors all devices on a network simultaneously and also monitors network traffic. Fused with artificial intelligence, machine learning and cloud-based security, this level of protection acts like a security blanket thrown over the home. It can identify and stop attacks in real time and assess the security status of new devices when they are attached to the smart home network.
Q2. Malware is one of the most common methods of stealing personally identifiable customer information. What can be done to protect unsuspecting customers from falling victim to such attacks?
A2. It’s a fundamental step but people need to use good antivirus software that uses both signature and behaviour-based detection. Signature-based detection takes care of the millions of known malware variants while behaviour-based detection identifies zero-day malware and stops it in its tracks as it tries to penetrate computers. Another important point is the need for awareness about email-based phishing attacks. This is a popular route for hackers and people need to be aware that emails requesting sensitive personal information such as payment card numbers, or providing links to web pages that also request personal information are scams designed to extract important financial information.
Q3. Data breaches are at an all-time high. What must businesses do to ensure protection of sensitive customer data?
A3. In addition to having fundamental security technologies in place businesses must adopt a zero-trust model across the entire enterprise, which in turn informs how they protect sensitive customer data. This is a ‘never trust, always verify’ approach. This then protects against a wide range of existing and evolving threats. For instance, under this model those responsible ask questions such as ‘is this third-party script on our website secure or can it be exploited by hackers?’ This detailed questioning approach requires investment but it makes all the difference as to whether sensitive data is stolen or kept safe.
Q4. With internet becoming ubiquitous, more and more kids are getting online. What precautions can parents take to ensure their kids’ safety online?
A4. Education and parental tools enable discreet monitoring of what children are doing online. Children receive cyber security training on stranger danger at school and it does no harm to reinforce this at home. One of the more disturbing perils is if children stumble across inappropriate content which can have an adverse impact on developing minds. Unhealthy peer pressure, social media bullying and posting risqué images are also important things to look out for. This is where parental controls are very helpful.
Q5. In the wake of urban futurism, what is the basic security hygiene that businesses and customers alike must maintain?
A5. Urban futurism is a short phrase for such big topic covering everything from
renewable energies, all kinds of web technology, blockchain, tactical urbanism, decentralised networks, autonomous cars and a lot more. People are getting excited at the potential of new technologies whether its town planners, civic designers, power companies and so on. However, to ensure basic security hygiene after asking the question ‘what can this technology do?’ a follow up question is required: ‘is it secure or is it vulnerable to hacking? And if so, how?’ This is less a requirement and more of an attitude. Without this questioning stance we are going to see an awful lot of new tech implementations that are ripe for hacking. And it’s not just singular devices we are talking about, it’s also about the networks they sit on and how these networks can be exploited.
Tech Interviews
TRACK24 UNVEILS ATLASNXT TO REDEFINE GLOBAL DUTY‑OF‑CARE AND RISK INTELLIGENCE

Exclusive interview with Andrew McInerney (CEO) and Ebad Abid (Head of Product), Track24
Can you introduce your company to us? What does AtlasNXT do?
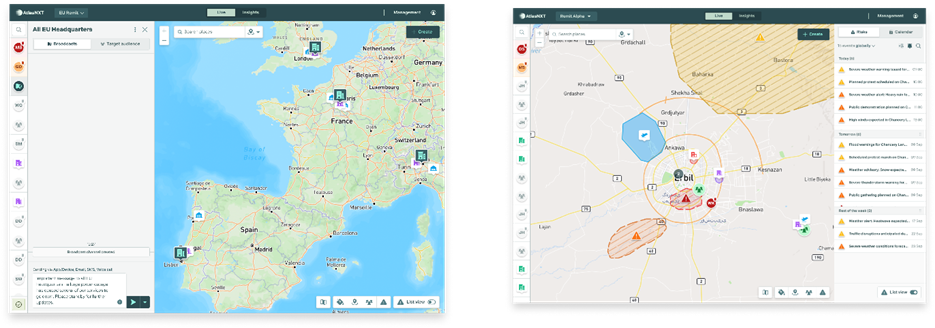
AtlasNXT, from TRACK24, is a duty-of-care location services and communication system. So, it enables a business to know where its people are and relate those people to the risks and other information they might face and then enables them to make decisions and communicate about to ensure the duty-of-care of their teams.
So, what inspired the founding of AtlasNXT and how does its mission differ from other duty-of-care and operational communication platforms?
TRACK24 was formed in 2004 as a location services company in high-risk environments, principally using satellite locations and satellite communication devices. And that remains one of our key differentiators, the ability to integrate satellite communications and satellite devices from any of the competitors. Since then, the world and the technology has moved on.
And in the last five years, we at TRACK24 have integrated lots of different, divergent bits of our software into AtlasNXT as a single software offering. And that provides those location services, not just to high-risk environments, but to GSM-capable and GPS-capable devices across any environment. So, where risk moves across place and time, then any business can use this, not just those ones in high risks as well.
So, it helps with travel risk management, it helps with precision communications to people, it reduces the amount of noise compared to the amount of signal that individuals get. So, precision information to the right people at the right time.
In your view, what is the biggest misconception organizations still have about modern duty-of-care technology?
We’ve come from a high-risk environment, from the most high-risk, and bring with us that sort of ethos of protection. Many organizations have come from a travel risk management environment, and therefore that tends to be diary predictions of where your diary says you’re going to be traveling that day, rather than precision location. And so, a lot of people bring with them the expectation that they get a generic travel risk management update, rather than something precise for their own movements, which changes as their own movements change.
So, the adaptability of a live tracking system enables that. The other key differentiator is the ability to maintain privacy. I’ve done that quick demonstration of the system.
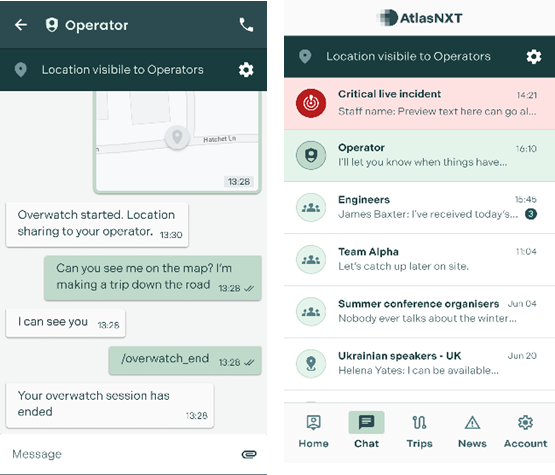
So, the individual knows when they’re able to be seen by their operation, by their operators, by their employer, and when they’re not, so they can maintain their privacy. And they only lose their privacy through consent. They press a button on the app and say, track me, or check me, overwatch me, or I’m in a panic mode, or by event, and they go inside a geofence, which their employer has put up on the map.
It might be their location, it might be a risk environment, and even then, the app tells the individual that you’re now visible to your operator. So, I think it’s key, the privacy element, and the live tracking, rather than any predictive element. Coming to the privacy part, AtlasNXT emphasizes privacy-first location-based communications.
How do you balance delivering critical information with user privacy concerns?
One of the challenges is, as you have said, is if you give the user the control, you won’t be able to actually support the user, because they’ll just switch it off. So, what we do is, we allow the system to share information, but we manage privacy through the visibility of the data that’s transferred, as opposed to switching it on and off, as most people do.
Because once you switch it off, the person’s MIA, and you can’t do anything to support them. They’re not going to get any notifications; we’re not going to know where they are. But if the system is always sharing, if their device is always sharing a location, or any form of notification with our system in the background, then we’re always able to reach them in the event something goes wrong.
The way we manage privacy is we essentially make them invisible, and they become visible by consent or event. So, one of the main things in data protection laws is legitimate interest. So, you should only ever have access to somebody’s information if you actually need it.
And so, you either give consent, that you can use my location data, or there’s a legitimate interest, such as they are in a potential area where there is a risk to them. At that point, we can reveal that location, and therefore, we’re always in control.
AtlasNXT integrates geofencing, precision messaging, and real-time operational intelligence. How do you see these capabilities?
Geofences themselves have evolved. First, they just used to be sort of a digital perimeter. Now, we’ve introduced smart geofences, which essentially allows you to track people coming in and out of that perimeter. What we also do is see what impacts that perimeter.
So, we have various intelligence feeds we integrate with, and you can see if a particular perimeter is impacted by that. Now, with AI, you can also then say, is that piece of intelligence relevant to the perimeter I’m monitoring? When you’re integrating with data providers, you’re probably getting a few thousand events a day. As humans, we can’t consume that much information, or if we can, we can’t comprehend what it means.
With the power of AI, we can summarize information and allow it to provide clarity. We can also use it to generate reports and deliver trend analysis.
For example, it can extrapolate that over X period of time, we’ve had X types of risk, which gives us the ability to predict future risk. So, if there is, for example, a civil conflict near a particular geofence, you’ll find that there are X amount of panic alarms pressed in the vicinity.
So, what AI will be able to do is allow us to forecast whether, you know, because of this event, we can expect this many people to be at risk. Which sends out early warnings automatically without human intervention being required.
From our engagement with customers, it’s clear that they want to maintain an operator in the decision loop. So, our approach to AI is that it does the heavy lifting, but only suggests options to the operator. This ensures a human remains in command and makes the critical decisions.
AI is powerful and can save a great deal of time, but we’re not at the point where life-and-death security decisions can be handed to a machine. It performs the groundwork while a human operator remains in control. One of its strengths is pattern recognition.
It can say to the operator, ‘we’re noticing this, do you want to take this action?’ It’s a co-pilot, not a pilot. It also improves efficiency, as AI can process large volumes of information instantly, reducing response times. The earlier an organisation can intervene, the safer its people are. AI summarises the situation, and the operator decides whether and how to act.
And how important was InterSec for you and this region, Middle East, for your company?
We’re headquartered in London with two subsidiary organizations in the Emirates and a country office in Iraq. The region is hugely important. It’s where we originated as a species and as a company. So, we started in 2004 in Baghdad, and we’ve always maintained a large presence in Iraq, Kurdistan and across the Middle East.
The world isn’t getting any easier. The world is not getting any less risky. The world is not getting any more certain. Risk is spreading and becoming quite unpredictable whether you’re the president of an independent nation or an independent nation that belongs to somebody else. Risk is coming to you around the globe.
Our services become more and more important and more relevant globally. The region of the Middle East is important because I think it’s a region that understands security in a very central way.
It was our first attendance at InterSec. We’re a software provider. From what I’ve seen so far, there’s lots of hardware providers.
And that means there’s lots of potential partners for us. We can integrate any of their systems into our system and make access control useful for decision support which is what we’re here to do.
Tech Interviews
Digital Sovereignty in Practice: What It Means for Enterprises Today

In our conversation with Ismail Ibrahim, General Manager, CEMEA at SUSE, we seek to understand the concept better along with his understanding of the industry and how enterprises in the UAE and Saudi Arabia can retain control in a rapidly evolving technology landscape.

What does “digital sovereignty” actually mean for an enterprise today, not in theory, but in day-to-day operations?
From an enterprise perspective, digital sovereignty becomes real the moment it changes what you do on a Monday morning. In practice, it means three things become operational requirements, not policy statements.
First, control over data. Not just where data is stored, but where it is processed, who can access it, and how you prove that in an audit. For many organizations in the UAE and Saudi Arabia, that is increasingly tied to sector rules, procurement requirements, and customer expectations.
You need the ability to keep sensitive workloads within national borders when required, but also to enable controlled data flows when innovation demands it. The important point is that sovereignty is not “ringfencing everything”. It is being deliberate about which data, which workloads and which dependencies must remain under your control.
Second, control over operations. Day-to-day, that looks like resilience and predictability: how quickly you can patch, how confidently you can recover, how consistently you can enforce policy across clusters, clouds and edge sites. This is where many enterprises discover that sovereignty is inseparable from operational excellence. If you cannot reliably manage your environments, you do not really control them.
Third, control over technology choices. This is where open source becomes practical, not ideological. When you build on open, enterprise-supported platforms, you are reducing dependency on opaque codebases and constraining the risk of being forced into a single vendor’s roadmap. Sovereignty is “choice by design”, because choice is what allows you to meet local requirements today and change course tomorrow.
That is why at SUSE we often frame sovereignty around pillars like control, choice and resilience, with autonomy as the long-term outcome. For enterprises, those pillars translate into everyday decisions: architecture, procurement, governance, patching, incident response and lifecycle management.
In the next three years, which will hurt enterprises more: security breaches, or being locked into the wrong technology stack?
It is not an either-or, because the two risks are increasingly connected.
A security breach is immediate and visible. It impacts customers, regulators, operations and reputation. But lock-in to the wrong stack can quietly increase breach risk over time, because it limits your ability to respond. If your architecture makes it hard to patch quickly, to segment workloads properly, to implement new controls, or to move sensitive workloads to a compliant environment, you have turned security into a dependency problem.
Over the next three years, I would say the most damaging scenario for many enterprises is not “breach versus lock-in”, but breach plus lock-in, where an organisation is under pressure and finds it cannot adapt fast enough.
This is exactly why sovereignty has moved into the C-suite and boardroom. Leaders are recognizing that digital sovereignty sits alongside cybersecurity and operational resilience as a strategic requirement. You need a risk-based approach to your data, workloads and support model, and you need the flexibility to change course.
Practically, in the UAE and Saudi Arabia, many CIOs are already building mixed environments across on-prem, sovereign cloud, hyperscalers and edge. The goal is not to avoid the cloud. The goal is to avoid a situation where strategic choices are dictated by a single vendor’s constraints. Open, enterprise-grade platforms help you keep the option to move, modernize or localize when needed, without rewriting everything from scratch.
As AI becomes embedded into infrastructure itself, do you believe enterprises are prepared to trust machines with operational decisions, or are we moving faster than governance allows?
In many cases, we are moving faster than governance, but that does not mean enterprises should slow down. It means they should modernize governance at the same pace as adoption.
The key is to separate hype from reality. “Trusting machines” does not mean handing over full autonomy overnight. For most enterprises, AI enters operations in stages.
Stage one is assistive intelligence, where AI helps surface insights, detect anomalies, recommend actions and reduce manual effort. This is where many organizations see quick operational value, especially in areas like observability, incident triage, capacity planning and security monitoring.
Stage two is bounded autonomy, where AI can execute actions within defined guardrails, such as automated scaling, routing, remediation playbooks, or policy-driven security responses. The governance requirement here is clear accountability: what is automated, under what conditions, with what approvals, and what audit trail.
Stage three is agentic operations, where more complex systems handle multi-step tasks across environments. This is the phase where governance must be mature, because the risk is not simply “wrong output”, it is unintended consequences across interconnected systems.
For the UAE and Saudi Arabia, readiness often depends on whether organisations have already done the foundations: standardised platforms, consistent policy enforcement, clean identity and access controls, and modern lifecycle management. If the foundation is fragmented, AI simply accelerates fragmentation.
This is why we are seeing strong interest in approaches that support governance by design, including the ability to run AI solutions in more controlled environments. In many regulated sectors, that includes air-gapped or restricted environments, where organizations want to adopt AI while keeping strict control of data movement and operational boundaries.
My view is that enterprises can absolutely trust AI in operations, but only when they treat trust as an engineering outcome: transparent systems, auditable controls, clear guardrails, and the ability to override. Governance is not a blocker. Governance is what makes adoption sustainable.
By 2030, will enterprises still control their infrastructure choices, or will hyperscalers and AI vendors effectively decide that for them?
Enterprises will control their choices if they design for control now. If they do not, the market will make the decision for them.
By 2030, the default buying motion will push organizations toward managed services, vertically integrated AI stacks, and increasingly opinionated platforms. That can deliver speed, but it can also compress choice, especially if your applications, data pipelines, security controls and operational tooling are tightly coupled to one vendor.
So the question is really about architecture and leverage. Enterprises that prioritise portability, standardization and open platforms will keep leverage. They can choose the right environment for each workload, based on performance, compliance, cost, and risk. Enterprises that ignore portability will find that “choice” exists on paper, but not in practice.
This is where digital sovereignty is often misunderstood. Sovereignty does not mean rejecting global technology. It means retaining the ability to make deliberate decisions about where workloads run and who controls the critical layers. Many leaders now talk about “glocal” strategies: using global innovation while maintaining local control and compliance where it matters.
At SUSE, our positioning has been consistent: open source supports sovereignty because it promotes transparency, portability and freedom from lock-in. That is not a slogan, it is a practical roadmap for keeping infrastructure choices in the hands of enterprises, not vendors.
If you had to offer one piece of advice to CIOs and policymakers in the UAE and Saudi Arabia navigating rapid digital transformation, what would it be?
My one piece of advice is this: treat sovereignty as an enabler of innovation, not a constraint, and build it into your operating model early.
For CIOs, that means starting with a clear map of your critical workloads and dependencies. Decide what must remain under national control, what can run on hyperscalers, what needs sovereign cloud options, and what requires special governance. Then standardize your foundations so you can enforce policy consistently. When sovereignty is engineered into the platform layer, transformation becomes faster, because you are not negotiating compliance from scratch every time you modernize an application.
For policymakers, it means continuing to create frameworks that encourage both innovation and trust. The UAE has taken a pragmatic approach in showing that openness and sovereignty do not have to conflict. When the policy environment supports clear requirements and predictable compliance expectations, enterprises can innovate with confidence.
And for both, there is a shared point: invest in skills and ecosystem capability. Sovereign outcomes are not delivered by policy alone, they are delivered by people, platforms, and partnerships. When you develop local talent, strengthen the partner ecosystem, and support enterprise-grade open source, you build resilience and long-term autonomy without slowing innovation.
Tech Interviews
SCALING PRACTICAL AI FOR RETAIL GROWTH IN THE GCC
Exclusive interview with Mark Turner, President EMEA, Rezolve Ai

What made Shoptalk Luxe Abu Dhabi a priority platform for Rezolve Ai this year?
For Rezolve Ai, Shoptalk Luxe Abu Dhabi brings together the right audience at the right moment. Luxury retailers in the region are no longer exploring ideas, they are making decisions and investing. It is a practical forum to exchange views with brands that are actively shaping their customer engagement and commerce strategies, and to have grounded conversations about what is working in real retail environments. Abu Dhabi also reflects how influential the region has become in global luxury thinking.
How is AI changing the way luxury retailers think about customer engagement today?
Luxury retailers are becoming far more intentional about how and when they engage customers. AI is helping them move away from broad personalisation toward more contextual, timely interactions that respect the brand experience. The focus is on supporting customers at key moments, whether online or in store, and ensuring engagement feels consistent and considered rather than automated or intrusive.
What distinguishes meaningful AI adoption in retail from short-term experimentation?
Retailers that see lasting value from AI are those that embed it into day-to-day operations rather than treating it as a standalone initiative. Meaningful adoption is driven by clear commercial goals, fast implementation, and solutions that work within existing systems and teams. Short-term experimentation tends to stall when it lacks ownership, scale, or a clear link to performance outcomes.
Why is the Middle East, and the UAE in particular, becoming increasingly important for luxury retail innovation?
The Middle East, and the UAE in particular, has created an environment where luxury retail innovation can move quickly. Consumers are digitally confident, infrastructure is strong, and there is a clear push at a national level to adopt advanced technologies. This combination allows retailers to implement and test new models at scale, which is why the region is increasingly influencing global luxury strategies.
Looking ahead, where do you see AI delivering the most value for luxury brands over the next few years?
The greatest value will come from AI that directly supports growth while reinforcing operational discipline. For luxury brands, that means more relevant engagement that improves conversion and loyalty, alongside better forecasting and inventory decisions that protect margins. The priority will be practical use of AI that enhances the customer experience without compromising brand integrity.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR12 months ago
VAR12 months agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Tech Interviews2 years ago
Tech Interviews2 years agoNavigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Trending5 months ago
Trending5 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 Tech News9 months ago
Tech News9 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive1 year ago
Automotive1 year agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms










