Tech Interviews
ON THE FAST LANE
By Editor
With internet speeds rising fast, many organizations are seeing their security appliances being left behind of the high speed bandwagon. Ajay Nawani, AVP Global Presale Operations at Cyberoam explains how the company can help
Why is it crucial for Cyberoam to launch the Next-Gen series of UTMs at this time?
The NG Series enables SOHO/SMBs networks to become future-ready as they move towards gigabit network infrastructure and high Internet speeds. However, today, their network security is not ready for these trends as few security vendors today offers them security throughputs or gigabit ports required for such networks. This is resulting in security becoming a bottleneck for the networks.
The need for Next-Gen UTM like the NG Series is being driven by several factors including the rise of superfast internet. We are seeing data moving at 10 times current internet speeds. Examples include Google which launched a 1000 Mbps ‘Google Fiber’ Internet service in the US. IDNet also launched 1000 Mbps Leased Line Business Ethernet Service in the UK. The MEA region cannot be further behind. There has also been a device explosion with on average multiple internet devices per user. In the enterprise, employee-owned smart devices are expected to reach 350mn by 2014, up from 150mn today. Cloud is also driving some of this need for fast internet. A lot of critical business applications and services are moving to the Web. Cloud computing is expected to generate more than $45.4 billion in revenue by 2015.
Why is it important then for security to move with the same speed as the rest of the network?
In many organizations, network infrastructure is moving to gigabit and anything less than gigabit is nearly obsolete. Security must also keep pace. With gigabit internet speeds to be available soon from ISPs and Telcos, the question is whether your security appliance can match these high Internet speeds and offer gigabit throughputs. With more devices per employee connecting to the IT network, the approach is changing from ‘Users’ to ‘Devices’. CIOs need to consider whether their security appliance can support any more number of Devices. The risk is that security becomes a bottleneck in the network. The most viable solution to tackle this is for organizations to move to future-ready security appliances. Cyberoam NG series offers ‘Future-Ready’ security with the fastest UTM appliances for SOHO and SMB segments, while offering Next-Generation firewall protection for large enterprises.
How is Cyberoam NG series then able to offer future-ready security?
The NG Series offers a combination of powerful hardware with superfast processing speed, a must for gigabit internet speeds, coupled with gigabit ports to enable gigabit speeds. Users also get nano-second security processing with multicore Gigahertz processors. The new NG-series also features a complete overhaul of appliance design outside, while inside we have included faster, next-gen memory and high capacity storage. This ensures superior quality for high performance and robustness. The design and components support high speed I/O throughput while also being able to withstand extreme environments.
A lot of regional Telcos are busy deploying 4G/LTE networks. What does this development portend for UTMs?
Our Next-Gen UTM products are 4G high-speed ready. We offer very easy deployment for high speed internet connection including VPN over 4G/LTE. This can be done through a simple USB modem plug-in into a Cyberoam UTM appliance. Further, our devices have auto detection of modem plug-in and plug-out making it easy and simple to deploy. The plug-and-play attributes of our Next-Gen UTMs continue with automatic failover to 4G/LTE WWAN connection as well as gateway failover over VPN. We’ve also extended this secure connectivity to support BYOD in organizations, offering Layer 8 Identity-based security for mobile devices. Users can thus securely connect their iPhones, iPad and Android devices to their corporate network through VPN.
With the new UTM, you have also included your own operating system, the Cyberoam OS. Why is this software different?
NG Series appliances come pre-loaded with Cyberoam OS – the most intelligent and powerful Cyberoam firmware till date. The new firmware tightly integrates with the hardware for network and crypto acceleration to deliver very high performance. The Cyberoam OS also extracts full performance from a multi-core platform, along with offering minimum latency and improved processing speed with use of optimized Interrupt rates and FastPath technology.
Please discuss a specific security application available with the new UTM
YouTube for Schools, an educational service from the video sharing giant, offers a huge repository of relevant and engaging content for students. However, in most instances, teachers cannot access these YouTube educational videos due to institutional security policies. Cyberoam’s Layer-8 controls on “YouTube for Schools” allows access to selected educational content while offering user (teachers/student) and group (school/class) level control after which it will generate user-based access reports. This application will also block all inappropriate and peripheral content such as ads, comments and links.
As virtualization grows in the region, what security challenges are organizations facing in this area?
Existing UTMs cannot scan Inter-VM traffic with externally based security hardware despite the fact that a single compromised virtual machine can infect the entire data center. Virtual machines face a higher risk of attacks on the hypervisor management console. Virtualized applications also face vulnerabilities from hackers. We have the right solutions for protecting virtualized servers from intrusion attacks. The Cyberoam Virtual Appliance resides on the virtual layer and scans all traffic inside the virtual environment.
Tech Interviews
STARKEY OMEGA AI – ONE OF THE MOST POWERFUL AND ADVANCED HEARING TECHNOLOGY TO EVER REACH MEA PATIENTS

In this exclusive interview, Giscard Bechara, Director of Starkey Middle East & Africa, reveals how Omega AI, the company’s most advanced hearing technology to date, is set to transform the lives of patients across the region, from smarter connectivity and real-time AI support to breakthrough health monitoring features.
Giscard, Starkey has just unveiled Omega AI, a bold claim to call it ‘superhuman.’ For patients here in the Middle East and Africa, what does that word actually mean in everyday life?
“Superhuman” isn’t marketing language for us, In the MEA region, our patients navigate some of the world’s most complex listening environments: bustling souks, multi-language family gatherings & noisy cities . Omega AI is engineered to mimic the auditory system in these very settings. When DNN 360 delivers 28% better speech intelligibility in a noisy environment, your brain is receiving a signal that is cleaner and crisp than ever before. That, to me, is a superhuman advantage, and it is now available to anyone wearing a Starkey hearing aid.
Tell us about DNN 360, the deep neural network at the heart of Omega AI. How is it different from the AI that patients may have heard about in other hearing aids?
Most hearing aids apply AI to a single task, perhaps noise reduction or voice enhancement. DNN 360 is the world’s first deep neural network that powers both directionality and spatial awareness simultaneously. Think of it this way: when you are in a restaurant in Dubai or a busy market in Egypt, you do not just want to hear the person in front of you, you want to know where every sound is coming from, so your brain can make sense of the scene around you. Our brain naturally detects sounds and acoustic queues to understand the environment that we are facing. DNN 360 provides up to 8 dB signal-to-noise ratio improvement for spatial awareness. That is a meaningful, real-world difference. And crucially, we achieve all of this without sacrificing battery life and performance.
For many patients in the MEA region, connectivity is critical, streaming TV, phone calls across different networks, even video consultations with specialists abroad. How does Omega AI address this?
Connectivity is a lifeline. We have made two significant advances. First, streaming via the StarLink Edge TV Streamer now starts and reconnects automatically for the TV, no more fumbling with settings or missing the beginning of a show. Second, and this is an industry first, we have introduced TeleHear AI. This feature uses generative AI to help patients resolve common hearing issues in real time, directly from their smartphone, with 93% predictive accuracy. For a patient in a remote area or in a country where specialist hearing clinics are hours away, this means they can troubleshoot and optimise their hearing experience without having to travel. That is transformative access.
You mentioned TeleHear AI, a 93% predictive accuracy rate is remarkable. Can you walk us through what that looks like for a patient who, say, notices their hearing feels muffled after a long flight from Riyadh to Johannesburg?
Absolutely. That patient opens the My Starkey app, describes what they are experiencing, and TeleHear AI analyses the situation using generative AI. It might recommend a specific listening programme for their current environment. the issue can be resolved without any professional intervention needed at that moment. In a region where patients often travel vast distances and cross multiple time zones, that kind of intelligent self-sufficiency is worth a lot.
Durability is a significant concern in our climate, from the humidity of coastal cities like Abu Dhabi and Lagos to the dust of the Sahara. How has Starkey engineered Omega AI for these realities?
We took this very seriously. Omega AI features waterproofing that has been tested to last 10 times longer than our previous coatings under the most demanding conditions, moisture, sweat, dust, temperature extremes. The MEA region presents environments that can be punishing for delicate electronics. Whether a patient is in a humid coastal city, working outdoors in the Gulf heat, or living in a dry, dusty climate, Omega AI is built to perform reliably day after day. This is not lab performance, it is field-tested durability. A hearing aid that fails in difficult conditions is not a solution; Omega AI is engineered to be there when patients need it most.
There are also new LED indicator lights, something that might seem like a small detail, Can you explain why they are there?
The LEDs are a helpful guide. The green and red indicator lights on our RIC RT and mRIC R devices confirm power status and Bluetooth connection briefly, simple, practical, and reassuring for patients and caregivers. Those same LEDs now double as a find-my-hearing-aid tool, an absolute industry first. If a patient misplaces a device, common in multi-room homes, during prayer, or when grandchildren are visiting, they can trigger the LEDs remotely through the app to locate it. For our older patients in the MEA region, and for the family members who support them, this feature provides real peace of mind.
Starkey has positioned Omega AI as a ‘healthable’, going beyond hearing to monitor overall wellness. Why is this vision particularly relevant for MEA patients?
The MEA region carries a significant burden of non-communicable disease, cardiovascular conditions, respiratory illness, balance disorders. These are the very health areas where Omega AI’s new wellness features add value beyond hearing. The automatic respiratory rate monitor is an industry first: it works silently in the background, tracking breathing patterns without the patient having to do anything. This can provide early indicators of conditions that affect breathing. Balance Builder, accessed through the My Starkey app, delivers targeted at-home exercises for stability and coordination, relevant for older adults at risk of falls, a major health concern across our region. We are not asking patients to add another wearable device. They are already wearing their hearing aids. We are simply making those hours work harder for their health. Omega Ai also counts your daily steps activity and motivates you to move and be active.
Access to specialist audiological care is uneven across the MEA region. How does Omega AI help bridge that gap, and what role does your team play on the ground?
This is a question close to my heart. In countries where audiologists are concentrated in major cities, patients in rural or underserved areas have historically faced significant barriers. Omega AI addresses this on two levels. Technologically, TeleHear AI means that a patient does not need to visit a clinic every time they have a question about their hearing aids. The generative AI guides them through real-time troubleshooting. And when remote fine-tuning is needed, our TeleHear platform connects them with their professional remotely. On the ground, Starkey MEA is committed to expanding our network of trained hearing professionals, our authorised partner clinics, and our educational programmes across the region. The technology opens the door, our people make sure patients can walk through it.
We know hearing loss carries a social stigma in certain communities across the Middle East and Africa. How does the design philosophy of Omega AI address that reality?
Stigma is real, and we design with that awareness. Omega AI devices are engineered to be discreet, modern, and, for those who prefer invisibility, designed to be worn comfortably without drawing attention. At the same time, we believe the best answer to stigma is performance. When a patient discovers they can follow a conversation at a family gathering for the first time in years, when they can engage fully in a business meeting, the hearing aid stops being something they hide and becomes something they value. Omega AI’s performance is so compelling that patients want to wear it. That shift in attitude is the most powerful antidote to stigma we have.
Finally, Giscard, what is your message to patients across the Middle East and Africa who are sitting on the fence about hearing care, or who have dismissed it as something for ‘other people’?
Hearing loss is not a sign of ageing or weakness, it is a health condition that affects one in five people globally, and the MEA region is no exception. Leaving it untreated has consequences that go far beyond the ears: increased social isolation, cognitive decline, missed opportunities at work and at home. Omega AI represents the most advanced hearing technology ever created, it gives patients a superhuman advantage in every listening environment they encounter. My message is simple: do not wait. A hearing assessment is the first step. Hearing tests are cheap, fast and not painful. It can change your life and save you money if you address your hearing loss early. In case hearing technology is needed, Omega AI is proof that it can be powerful, intelligent, beautiful, and life-changing. Visit your audiologists. Your world deserves to be heard fully.
Tech Interviews
TRACK24 UNVEILS ATLASNXT TO REDEFINE GLOBAL DUTY‑OF‑CARE AND RISK INTELLIGENCE

Exclusive interview with Andrew McInerney (CEO) and Ebad Abid (Head of Product), Track24
Can you introduce your company to us? What does AtlasNXT do?
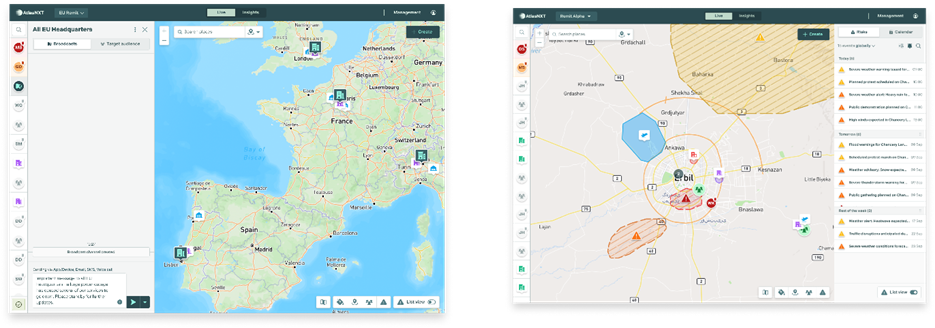
AtlasNXT, from TRACK24, is a duty-of-care location services and communication system. So, it enables a business to know where its people are and relate those people to the risks and other information they might face and then enables them to make decisions and communicate about to ensure the duty-of-care of their teams.
So, what inspired the founding of AtlasNXT and how does its mission differ from other duty-of-care and operational communication platforms?
TRACK24 was formed in 2004 as a location services company in high-risk environments, principally using satellite locations and satellite communication devices. And that remains one of our key differentiators, the ability to integrate satellite communications and satellite devices from any of the competitors. Since then, the world and the technology has moved on.
And in the last five years, we at TRACK24 have integrated lots of different, divergent bits of our software into AtlasNXT as a single software offering. And that provides those location services, not just to high-risk environments, but to GSM-capable and GPS-capable devices across any environment. So, where risk moves across place and time, then any business can use this, not just those ones in high risks as well.
So, it helps with travel risk management, it helps with precision communications to people, it reduces the amount of noise compared to the amount of signal that individuals get. So, precision information to the right people at the right time.
In your view, what is the biggest misconception organizations still have about modern duty-of-care technology?
We’ve come from a high-risk environment, from the most high-risk, and bring with us that sort of ethos of protection. Many organizations have come from a travel risk management environment, and therefore that tends to be diary predictions of where your diary says you’re going to be traveling that day, rather than precision location. And so, a lot of people bring with them the expectation that they get a generic travel risk management update, rather than something precise for their own movements, which changes as their own movements change.
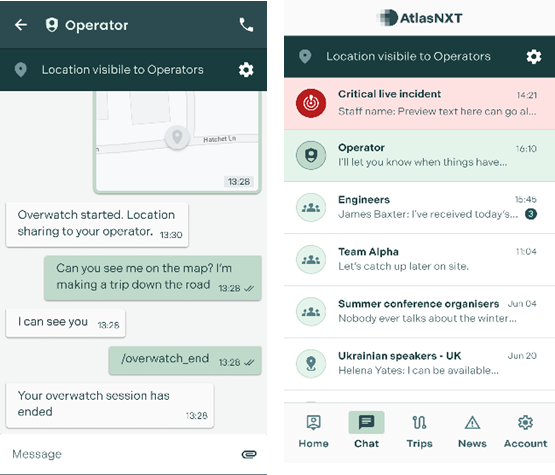
So, the adaptability of a live tracking system enables that. The other key differentiator is the ability to maintain privacy. I’ve done that quick demonstration of the system.
So, the individual knows when they’re able to be seen by their operation, by their operators, by their employer, and when they’re not, so they can maintain their privacy. And they only lose their privacy through consent. They press a button on the app and say, track me, or check me, overwatch me, or I’m in a panic mode, or by event, and they go inside a geofence, which their employer has put up on the map.
It might be their location, it might be a risk environment, and even then, the app tells the individual that you’re now visible to your operator. So, I think it’s key, the privacy element, and the live tracking, rather than any predictive element. Coming to the privacy part, AtlasNXT emphasizes privacy-first location-based communications.
How do you balance delivering critical information with user privacy concerns?
One of the challenges is, as you have said, is if you give the user the control, you won’t be able to actually support the user, because they’ll just switch it off. So, what we do is, we allow the system to share information, but we manage privacy through the visibility of the data that’s transferred, as opposed to switching it on and off, as most people do.
Because once you switch it off, the person’s MIA, and you can’t do anything to support them. They’re not going to get any notifications; we’re not going to know where they are. But if the system is always sharing, if their device is always sharing a location, or any form of notification with our system in the background, then we’re always able to reach them in the event something goes wrong.
The way we manage privacy is we essentially make them invisible, and they become visible by consent or event. So, one of the main things in data protection laws is legitimate interest. So, you should only ever have access to somebody’s information if you actually need it.
And so, you either give consent, that you can use my location data, or there’s a legitimate interest, such as they are in a potential area where there is a risk to them. At that point, we can reveal that location, and therefore, we’re always in control.
AtlasNXT integrates geofencing, precision messaging, and real-time operational intelligence. How do you see these capabilities?
Geofences themselves have evolved. First, they just used to be sort of a digital perimeter. Now, we’ve introduced smart geofences, which essentially allows you to track people coming in and out of that perimeter. What we also do is see what impacts that perimeter.
So, we have various intelligence feeds we integrate with, and you can see if a particular perimeter is impacted by that. Now, with AI, you can also then say, is that piece of intelligence relevant to the perimeter I’m monitoring? When you’re integrating with data providers, you’re probably getting a few thousand events a day. As humans, we can’t consume that much information, or if we can, we can’t comprehend what it means.
With the power of AI, we can summarize information and allow it to provide clarity. We can also use it to generate reports and deliver trend analysis.
For example, it can extrapolate that over X period of time, we’ve had X types of risk, which gives us the ability to predict future risk. So, if there is, for example, a civil conflict near a particular geofence, you’ll find that there are X amount of panic alarms pressed in the vicinity.
So, what AI will be able to do is allow us to forecast whether, you know, because of this event, we can expect this many people to be at risk. Which sends out early warnings automatically without human intervention being required.
From our engagement with customers, it’s clear that they want to maintain an operator in the decision loop. So, our approach to AI is that it does the heavy lifting, but only suggests options to the operator. This ensures a human remains in command and makes the critical decisions.
AI is powerful and can save a great deal of time, but we’re not at the point where life-and-death security decisions can be handed to a machine. It performs the groundwork while a human operator remains in control. One of its strengths is pattern recognition.
It can say to the operator, ‘we’re noticing this, do you want to take this action?’ It’s a co-pilot, not a pilot. It also improves efficiency, as AI can process large volumes of information instantly, reducing response times. The earlier an organisation can intervene, the safer its people are. AI summarises the situation, and the operator decides whether and how to act.
And how important was InterSec for you and this region, Middle East, for your company?
We’re headquartered in London with two subsidiary organizations in the Emirates and a country office in Iraq. The region is hugely important. It’s where we originated as a species and as a company. So, we started in 2004 in Baghdad, and we’ve always maintained a large presence in Iraq, Kurdistan and across the Middle East.
The world isn’t getting any easier. The world is not getting any less risky. The world is not getting any more certain. Risk is spreading and becoming quite unpredictable whether you’re the president of an independent nation or an independent nation that belongs to somebody else. Risk is coming to you around the globe.
Our services become more and more important and more relevant globally. The region of the Middle East is important because I think it’s a region that understands security in a very central way.
It was our first attendance at InterSec. We’re a software provider. From what I’ve seen so far, there’s lots of hardware providers.
And that means there’s lots of potential partners for us. We can integrate any of their systems into our system and make access control useful for decision support which is what we’re here to do.
Tech Interviews
Digital Sovereignty in Practice: What It Means for Enterprises Today

In our conversation with Ismail Ibrahim, General Manager, CEMEA at SUSE, we seek to understand the concept better along with his understanding of the industry and how enterprises in the UAE and Saudi Arabia can retain control in a rapidly evolving technology landscape.

What does “digital sovereignty” actually mean for an enterprise today, not in theory, but in day-to-day operations?
From an enterprise perspective, digital sovereignty becomes real the moment it changes what you do on a Monday morning. In practice, it means three things become operational requirements, not policy statements.
First, control over data. Not just where data is stored, but where it is processed, who can access it, and how you prove that in an audit. For many organizations in the UAE and Saudi Arabia, that is increasingly tied to sector rules, procurement requirements, and customer expectations.
You need the ability to keep sensitive workloads within national borders when required, but also to enable controlled data flows when innovation demands it. The important point is that sovereignty is not “ringfencing everything”. It is being deliberate about which data, which workloads and which dependencies must remain under your control.
Second, control over operations. Day-to-day, that looks like resilience and predictability: how quickly you can patch, how confidently you can recover, how consistently you can enforce policy across clusters, clouds and edge sites. This is where many enterprises discover that sovereignty is inseparable from operational excellence. If you cannot reliably manage your environments, you do not really control them.
Third, control over technology choices. This is where open source becomes practical, not ideological. When you build on open, enterprise-supported platforms, you are reducing dependency on opaque codebases and constraining the risk of being forced into a single vendor’s roadmap. Sovereignty is “choice by design”, because choice is what allows you to meet local requirements today and change course tomorrow.
That is why at SUSE we often frame sovereignty around pillars like control, choice and resilience, with autonomy as the long-term outcome. For enterprises, those pillars translate into everyday decisions: architecture, procurement, governance, patching, incident response and lifecycle management.
In the next three years, which will hurt enterprises more: security breaches, or being locked into the wrong technology stack?
It is not an either-or, because the two risks are increasingly connected.
A security breach is immediate and visible. It impacts customers, regulators, operations and reputation. But lock-in to the wrong stack can quietly increase breach risk over time, because it limits your ability to respond. If your architecture makes it hard to patch quickly, to segment workloads properly, to implement new controls, or to move sensitive workloads to a compliant environment, you have turned security into a dependency problem.
Over the next three years, I would say the most damaging scenario for many enterprises is not “breach versus lock-in”, but breach plus lock-in, where an organisation is under pressure and finds it cannot adapt fast enough.
This is exactly why sovereignty has moved into the C-suite and boardroom. Leaders are recognizing that digital sovereignty sits alongside cybersecurity and operational resilience as a strategic requirement. You need a risk-based approach to your data, workloads and support model, and you need the flexibility to change course.
Practically, in the UAE and Saudi Arabia, many CIOs are already building mixed environments across on-prem, sovereign cloud, hyperscalers and edge. The goal is not to avoid the cloud. The goal is to avoid a situation where strategic choices are dictated by a single vendor’s constraints. Open, enterprise-grade platforms help you keep the option to move, modernize or localize when needed, without rewriting everything from scratch.
As AI becomes embedded into infrastructure itself, do you believe enterprises are prepared to trust machines with operational decisions, or are we moving faster than governance allows?
In many cases, we are moving faster than governance, but that does not mean enterprises should slow down. It means they should modernize governance at the same pace as adoption.
The key is to separate hype from reality. “Trusting machines” does not mean handing over full autonomy overnight. For most enterprises, AI enters operations in stages.
Stage one is assistive intelligence, where AI helps surface insights, detect anomalies, recommend actions and reduce manual effort. This is where many organizations see quick operational value, especially in areas like observability, incident triage, capacity planning and security monitoring.
Stage two is bounded autonomy, where AI can execute actions within defined guardrails, such as automated scaling, routing, remediation playbooks, or policy-driven security responses. The governance requirement here is clear accountability: what is automated, under what conditions, with what approvals, and what audit trail.
Stage three is agentic operations, where more complex systems handle multi-step tasks across environments. This is the phase where governance must be mature, because the risk is not simply “wrong output”, it is unintended consequences across interconnected systems.
For the UAE and Saudi Arabia, readiness often depends on whether organisations have already done the foundations: standardised platforms, consistent policy enforcement, clean identity and access controls, and modern lifecycle management. If the foundation is fragmented, AI simply accelerates fragmentation.
This is why we are seeing strong interest in approaches that support governance by design, including the ability to run AI solutions in more controlled environments. In many regulated sectors, that includes air-gapped or restricted environments, where organizations want to adopt AI while keeping strict control of data movement and operational boundaries.
My view is that enterprises can absolutely trust AI in operations, but only when they treat trust as an engineering outcome: transparent systems, auditable controls, clear guardrails, and the ability to override. Governance is not a blocker. Governance is what makes adoption sustainable.
By 2030, will enterprises still control their infrastructure choices, or will hyperscalers and AI vendors effectively decide that for them?
Enterprises will control their choices if they design for control now. If they do not, the market will make the decision for them.
By 2030, the default buying motion will push organizations toward managed services, vertically integrated AI stacks, and increasingly opinionated platforms. That can deliver speed, but it can also compress choice, especially if your applications, data pipelines, security controls and operational tooling are tightly coupled to one vendor.
So the question is really about architecture and leverage. Enterprises that prioritise portability, standardization and open platforms will keep leverage. They can choose the right environment for each workload, based on performance, compliance, cost, and risk. Enterprises that ignore portability will find that “choice” exists on paper, but not in practice.
This is where digital sovereignty is often misunderstood. Sovereignty does not mean rejecting global technology. It means retaining the ability to make deliberate decisions about where workloads run and who controls the critical layers. Many leaders now talk about “glocal” strategies: using global innovation while maintaining local control and compliance where it matters.
At SUSE, our positioning has been consistent: open source supports sovereignty because it promotes transparency, portability and freedom from lock-in. That is not a slogan, it is a practical roadmap for keeping infrastructure choices in the hands of enterprises, not vendors.
If you had to offer one piece of advice to CIOs and policymakers in the UAE and Saudi Arabia navigating rapid digital transformation, what would it be?
My one piece of advice is this: treat sovereignty as an enabler of innovation, not a constraint, and build it into your operating model early.
For CIOs, that means starting with a clear map of your critical workloads and dependencies. Decide what must remain under national control, what can run on hyperscalers, what needs sovereign cloud options, and what requires special governance. Then standardize your foundations so you can enforce policy consistently. When sovereignty is engineered into the platform layer, transformation becomes faster, because you are not negotiating compliance from scratch every time you modernize an application.
For policymakers, it means continuing to create frameworks that encourage both innovation and trust. The UAE has taken a pragmatic approach in showing that openness and sovereignty do not have to conflict. When the policy environment supports clear requirements and predictable compliance expectations, enterprises can innovate with confidence.
And for both, there is a shared point: invest in skills and ecosystem capability. Sovereign outcomes are not delivered by policy alone, they are delivered by people, platforms, and partnerships. When you develop local talent, strengthen the partner ecosystem, and support enterprise-grade open source, you build resilience and long-term autonomy without slowing innovation.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR12 months ago
VAR12 months agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Trending5 months ago
Trending5 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 Tech Interviews2 years ago
Tech Interviews2 years agoNavigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Tech News9 months ago
Tech News9 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive2 years ago
Automotive2 years agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms











