Cover Story
Genetec Highlights Top Data Privacy Practices for Physical Security Leaders

Genetec, a leading technology provider of unified security, public safety, operations, and business intelligence solutions, shared a comprehensive set of data protection best practices to help physical security leaders protect privacy, safeguard data, and enable trust without compromising security.
This initiative comes as a response to the escalating importance of data security in an increasingly interconnected digital landscape. By prioritizing privacy, organizations can effectively contribute to a safer digital and physical landscape for all.
“Organizations should never have to choose between data privacy and security. By equipping physical security professionals with these essential strategies, Genetec is spearheading a paradigm shift towards a more resilient and trustworthy security ecosystem. It is an ongoing process, and organizations should regularly update protocols, stay informed and continuously educate their teams on best practices”, said Firas Jadalla, Regional Director – Middle East, Turkey and Africa (META) Genetec.
Genetec recommends organizations ensure their security systems respect data privacy by:
1. Collecting and Storing Only What You Need:
A fundamental rule of data security is to collect and store only essential information. The potential impact of a security breach can be reduced by minimizing stored data. It’s important to regularly review and audit data and dispose of unnecessary information responsibly.
2. Limiting Access to Sensitive Data:
Enhancing data security involves restricting access to sensitive information. Genetec recommends implementing data-sharing best practices, such as removing personally identifiable information to safeguard individual privacy. Techniques for anonymizing personal information while retaining its utility include:
- Randomization (adding noise to numerical values such as an individual’s age or income),
- pseudonymization (such as replacing names with unique identifiers), tokenization (such as replacing credit card numbers with tokens that have no direct correlation to the original numbers),
- generalization (such as converting exact birthdates to age ranges),
- and data masking (showing only the first few digits of a phone number).
3. Ensuring Privacy without Compromising Evidence:
By making use of technologies such as KiwiVision™ Privacy Protector, organizations can automatically anonymize images of people, so they can continue to survey surveillance footage while respecting privacy. This technology also offers an additional layer of security that ensures only authorized users can “unlock” and view unmasked footage while maintaining an audit trail.
4. Being Transparent and Get User Consent:
Building trust through transparency and user consent is essential. It’s important to clearly communicate with users about the data collection process, promoting informed decisions. Organizations should also gain explicit consent before collecting and processing data.
5. Choosing a Reliable Data Storage Provider:
Organizations should select a data storage provider carefully, ensuring a clear understanding of data storage, handling, and sharing practices. If using third-party services, organizations should demand strong security measures and reliable data handling practices. Establish who “owns” any data stored in the cloud, and any rights/privileges associated with the use or disclosure of any information.
6. Establishing Strong Policies:
To ensure long-term data safety, Genetec recommends putting in place robust policies across the organization. Enforcing a transparent chain of custody through technology, such as a Digital Evidence Management System (DEMS), ensures accountability and traceability at every stage of the data lifecycle.
Cover Story
The Shift to Unified Content Workflows Is Redefining Enterprise Media!


Walk into any modern content setup today, whether it’s a podcast studio, a corporate webinar room, or a hybrid event environment, and you’ll see a familiar pattern, one that reflects how fragmented the content production stack has become.
A microphone connected to an interface.
An interface connected to a laptop.
A laptop running multiple layers of software to mix, switch, stream, and record.
It works, but it’s rarely seamless.
Because the biggest challenge in content creation today isn’t access to tools, it’s understanding how they all fit together.
The Real Problem: Too Many Tools, Too Little Clarity
The rise of podcasting and video content has created a new kind of friction. Users are no longer asking what they can create; they are asking how to make the tools work together.
Recording audio separately, syncing video later, transferring large files to high-end machines, and relying on multiple software layers have become the default workflow. It works, but it is inefficient, expensive, and prone to failure.
The expanding ecosystem of devices, features, and formats has made even basic setup decisions unnecessarily complex.
When it comes to products from RØDE, users & creators already recognize the product’s potential to simply clarify and help elevate the overall workflow experience.
From Tools to Unified Systems
This is where the shift begins to stand out.
What we are seeing is not simply the addition of new features, but the consolidation of functions.
Mixer. Recorder. Audio interface. Video switcher. Stream encoder.
What traditionally required a stack of hardware and software is now being brought into a single console environment.
For creators, that simplifies production.
For enterprises, it changes how content infrastructure is designed.
As this shift gains momentum, it is also being acknowledged at a leadership level.

“Real innovation isn’t about adding more; it’s about removing friction and enhancing workflows.
Kalinda Atkinson,
With the introduction of platforms like the RØDECaster Video, we’re starting to see audio and video unified in one system, unlocking faster, more focused creative output.”
Global Marketing Director, RØDE
Why This Matters Beyond Creators
This shift is not limited to podcasters or streamers. Enterprises are increasingly building in-house content studios, executive communication channels, internal video platforms, and hybrid event capabilities as part of their broader communication strategy.

In these environments, complexity quickly becomes a bottleneck. Multiple tools often translate into longer setup times, increased points of failure, and a growing dependency on technical operators to manage what should ideally be straightforward workflows.
A unified system begins to reduce that friction, allowing teams to focus less on managing the process and more on the output itself.
The End of the Laptop-Centric Setup
One of the most significant changes is subtle: the laptop is no longer central.
With recording, streaming, and switching built directly into the console, content can now be produced without relying on external software or intermediary platforms. Audio and video routing happens natively within the system, removing the need to manage multiple layers of tools.
This, in turn, reduces reliance on tools like OBS Studio and lowers the need for high-performance machines in the production chain.
Broadcast Capabilities, Simplified
Features that were once limited to broadcast environments are now being integrated directly into compact systems. Capabilities such as multi-camera switching, ISO recording with separate tracks for each input, audio-based automatic switching between speakers, and network-driven video workflows like NDI are no longer confined to high-end production setups.
For enterprise teams, this translates into professional-grade production without the need for dedicated control rooms or complex broadcast infrastructure.
Modularity Signals Long-Term Thinking
Another important shift lies in how these systems evolve over time.
With expansion options such as adding video capabilities to existing audio consoles, RØDE is enabling a more modular approach to production. Instead of replacing entire systems, users can extend them based on their needs.
This becomes particularly relevant for organizations that may begin with audio-first content using consoles such as the RØDECaster Duo or RØDECaster Pro II, gradually expanding into video production with consoles such as RØDECaster Video, RØDECaster Video S, or even the RØDECaster Core, and scaling internal media capabilities over time. The result is a more flexible investment model that reduces upfront costs while supporting long-term growth.

A Shift in the Competitive Landscape
On the surface, this still appears to sit within the audio hardware category. In practice, however, it competes with something far broader.
As these systems begin to handle capture, processing, and output within a single environment, they start to overlap with production software ecosystems, video switching platforms, and content workflow tools.
The implication is clear: when orchestration happens within the system itself, the need for external layers begins to diminish.
The Opportunity Ahead
As the layers of complexity fade, creators will have more time for creative storytelling and less time worrying about the setup.
The new products and technology from RØDE not only remove setup barriers, but they also enable creators & enterprises to operate at a full professional standard, accelerating both the creativity and innovation ecosystems.

Srijith KN covers enterprise technology, media infrastructure, and digital transformation across the Middle East.
Cover Story
Cloud waste isn’t about Visibility it’s about Timing, says Atmoz CEO

“Cloud waste isn’t created by bad engineers. It’s created by systems that show problems too late. Once I saw that, it became clear, the solution wasn’t better reporting. It was prevention.” – Atmoz CEO Yael Shatzky
Yael Shatzky didn’t set out to build a company around cloud costs. What she noticed, after more than 25 years across enterprise technology, product marketing, and growth at organisations including Amdocs and Microsoft’s R&D ecosystem, was a pattern.
Not just rising cloud spend, but a deeper structural disconnect in how it’s managed.
If you were introducing yourself and Atmoz to someone outside tech, where would you begin?
I’d say I’m building a company that changes how people think about waste—specifically cloud and AI waste.
Imagine a house where electricity prices constantly change depending on what you use and when, but no one knows the cost. Lights stay on, AC runs all day, and while you know you’re wasting about 30%, you have no way to prevent it. The only signal you get is last month’s bill.
That’s how companies operate in the cloud today.
Atmoz changes that by bringing cost awareness into the moment decisions are made, helping teams make smarter choices without disrupting how they work. The result is simple: waste is prevented before it happens.
What is the core problem Atmoz is solving—and where has the market gone wrong?
The market has focused on visibility, dashboards and reports that explain what already happened.
But the problem isn’t visibility.
It’s timing.
By the time companies see the data, the money is already spent and systems are already in production. Even with perfect visibility, nothing changes.
Atmoz works at the moment engineers are building, engaging them with immediate, simple recommendations that don’t slow them down. That’s where prevention becomes possible.
What does ‘AI-first’ product development look like at Atmoz?
We built a data foundation that reconstructs cost signals as resources are created, before billing data exists. That’s the hard part.
On top of that, we use AI where it matters most: interaction and execution. Our AI agent takes accurate, contextual data and delivers actionable recommendations directly within developer workflows.
Because the system is grounded in precise data, the guidance isn’t just intelligent, it’s reliable and immediately usable.
What are the biggest challenges in getting engineers to trust AI-driven recommendations?
Interestingly, it’s not trust in AI, it’s the belief that prevention is even possible.
For years, companies have been told they can reduce costs, yet around 30% of cloud spend is still wasted. That’s because most tools analyse waste after it happens, they don’t stop it.
Once engineers see an issue flagged in real time, with clear context and a simple fix, the skepticism disappears. It becomes tangible.
What is one leadership mistake that fundamentally changed how you operate?
Focusing too much on the product, and not enough on marketing early on.
Great products don’t speak for themselves, especially when you’re creating a new category. Marketing isn’t something you layer on later; it shapes how the product is understood and adopted. Starting early makes a significant difference.
Where do you see the biggest inefficiencies today?
The biggest inefficiency is the disconnect between engineering decisions and their financial impact.
Every time a developer deploys infrastructure or triggers an AI workload, they’re making a financial decision, without visibility into its cost implications.
AI is amplifying this. Costs are more volatile, and traditional feedback loops can’t keep up.
Atmoz brings cost awareness into that decision point, making efficiency part of the engineering discipline, much like security became over time.
At this stage, how do you define success?
Success isn’t a single milestone, it’s a series of moments.
Signing a new customer. Launching a capability that impacts spend. Getting a call from a customer excited because they just saved $30K on something they didn’t even know was happening.
Those moments are what drive us forward.
You’re defining a new category. What does it take to change long-held assumptions?
It starts with conviction. You’re asking people to question something they’ve accepted as normal.
But conviction alone isn’t enough, proof is everything. Category change happens when someone sees it working in their own environment and has that “aha” moment.
That’s why we focus on immediate, tangible value. When waste is prevented in real time, the mindset shift follows naturally.
Resilience also matters. When you challenge established models, you will be dismissed. The key is to stay grounded in the problem and keep showing evidence.
Has the industry been solving cloud waste the wrong way? Why hasn’t it changed?
I wouldn’t say wrong, FinOps tools solved the problem they were designed for. They brought visibility and governance, which was critical.
But they were built on the assumption that cost is something you analyse after it happens.
Today, cost is created instantly, when infrastructure is provisioned or AI workloads run. But feedback still comes later. That gap is the issue.
What’s changed is the pace of engineering. With AI, decisions are faster and costs are more dynamic. What used to be inefficient is now unsustainable.
That’s why prevention isn’t just an improvement, it’s becoming essential.
How will engineering teams work differently in five years?
Cost will no longer be treated as something external, owned by finance. It will become part of the engineering feedback loop, like performance or reliability.
Atmoz brings that awareness into everyday workflows, guiding better decisions without adding friction.
Over time, this shifts behaviour. Waste isn’t something you detect and fix later, it simply doesn’t get created.
The result is not just lower cost, but faster teams, better decisions, and more room to innovate.
Cover Story
Huawei MatePad Mini: A Tablet That Feels Like a Real Notebook


Huawei’s compact tablet feels less like a gadget and more like a thoughtfully designed digital notebook, blending portability with everyday productivity.
I have been using Huawei’s MatePad 11.5 S for a while now for writing, editing, and most of my day-to-day journalistic work. It has turned out to be a surprisingly capable productivity device. So, when the MatePad Mini arrived, I was curious to see how Huawei would translate that experience into a much smaller form factor.
Reviewed By: Srijith KN, Senior Editor, Integrator
Design and Accessories
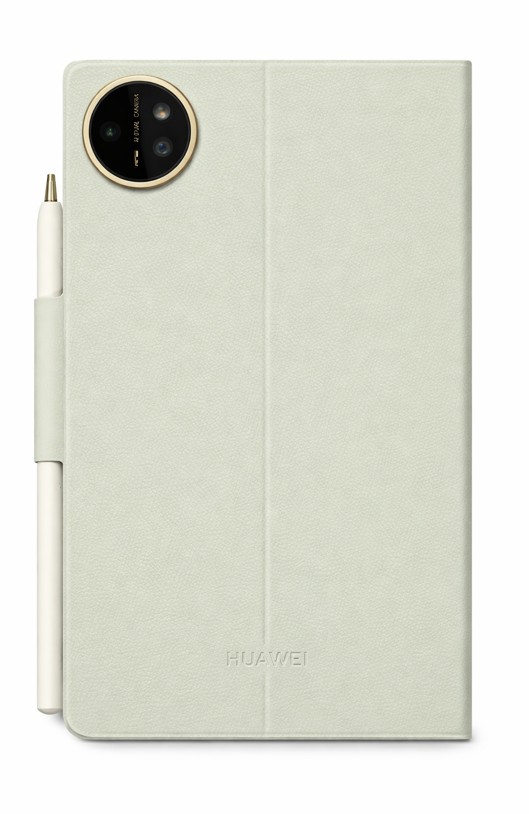
The first thing that stood out during the unboxing was not just the device, its accessories! Huawei has clearly put thought into the overall experience. The tablet ships with well-designed cases, including a transparent option and a diary-style booklet cover.
The diary cover, in particular, immediately felt right to me. It makes the tablet feel less like a gadget and more like a compact notebook you would carry every day. There is a certain familiarity to it, almost like picking up a journal rather than a device.
Huawei also continues to include a charger in the box, and this one comes with a 66W unit, a thoughtful touch at a time when many brands have moved away from bundling one altogether.
Everyday Portability

The 8.8 inch tablet immediately feels comfortable in the hand. It is extremely light and compact, measuring just 5.1 mm thick and weighing around 255 grams. That portability is noticeable right away.
In many ways, it feels closer to carrying a paperback than a traditional tablet. I currently use the Nothing Phone 3 as my daily device, and at times even that feels heavier than this. The MatePad Mini, on the other hand, almost disappears in your hands.
Huawei is also using a magnesium alloy body here, which keeps the device light without compromising on rigidity. Given how thin it is, that added structural strength feels reassuring.
A Paper Like Experience That Works
Last night, I found myself reading long articles on it for hours without feeling any strain. That is where the device really begins to make sense.

It genuinely feels like a digital paper booklet, built for reading, note-taking, writing, or quickly catching up on work while on the move. The green variant, in particular, features Huawei’s PaperMatte display, and it is easily one of the most distinctive aspects of this device.
Huawei claims the display reduces up to 99 percent of ambient light interference, and in real-world use, that translates into a noticeably glare-free experience. Even under indoor lighting, reflections are minimal, and the screen remains comfortable to look at for extended periods.
At the same time, it does not compromise on performance. With up to 1800 nits of brightness, a 120Hz refresh rate, and a wide color gamut, the display manages to balance readability with visual richness, something that is not easy to get right in smaller devices.
There is also an eBook mode that shifts the display into a black and white, paper like view, along with other settings designed to reduce eye strain during longer reading sessions. Additional options like eye comfort and sleep mode further support extended use.
Writing and Creativity
I also spent some time using the M Pencil for quick notes, and the experience feels surprisingly close to paper. Coming from the MatePad 11.5 S, Huawei continues to deliver one of the better stylus experiences in this space.

The M Pencil Pro adds more depth to the experience than expected. With different tip options and subtle haptic feedback, writing feels more tactile and intentional, rather than just tapping on glass.
Paired with the updated Huawei Notes app, the experience becomes more refined. Features like handwriting enhancement subtly improve legibility without taking away the personal feel of your writing, making it especially useful for quick notes and longer-form thinking.
Hardware and Performance
The MatePad Mini packs a 6400 mAh battery with support for fast charging, capable of going from zero to full in about an hour. On paper, it looks promising, though I will reserve judgment until I have spent more time with it.

On the hardware side, it includes a 50MP rear camera and a 32MP front camera, along with stereo speakers, Wi-Fi 7, USB-C 3.0, and a fingerprint sensor, something I wish Huawei had included on the MatePad 11.5 S as well.
Editor’s Perspective
Whenever I am seen using a Huawei device, the first question that comes up from people around me is usually about the ecosystem, particularly about Google services.
I too had similar concerns earlier, but having used Huawei devices for a while now, the experience has been smoother than expected. HarmonyOS feels clean and fluid, and tools like GBox make it possible to access most essential apps. Even for someone deeply tied to Google services, it has been more manageable than I initially thought.
What becomes clearer over time is that this is not just a smaller tablet. It sits somewhere between an eBook reader and a productivity device, built for focused, everyday use.
The MatePad Mini does not feel like Huawei shrinking a tablet. It feels like a refinement of how a compact device should actually be used. Its notebook-like form, paper-inspired display, and practical accessories make it easy to carry, pick up, and use throughout the day.
It is still early days, but the first impressions are strong. In a crowded tablet market, this feels like one of the more purposeful and interesting form-factor than the other compacts that we have seen in a while.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR1 year ago
VAR1 year agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Trending6 months ago
Trending6 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-
Tech Interviews2 years ago
Navigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Tech News10 months ago
Tech News10 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive2 years ago
Automotive2 years agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms












