Tech Features
5 Urgent Questions About Healthcare Network Cybersecurity in the Middle East

By Emad Fahmy, Director of Systems Engineering, NETSCOUT
As the Middle East’s healthcare sector increasingly embraces digital transformation, it faces a growing range of cybersecurity challenges. Cyberattacks, particularly ransomware, are becoming a significant threat to healthcare organisations in the region. According to KPMG, the frequency of ransomware incidents within the healthcare sector in the Middle East is on the rise, with data breaches leading to substantial financial and reputational damage. Protecting patient data and ensuring the integrity of healthcare networks is paramount in this evolving landscape.
Here are five critical questions healthcare organisations in the Middle East must address to secure their networks and data against the growing threat of cyberattacks:
- Are We Adequately Prepared for Ransomware Attacks?
Ransomware is a persistent threat to healthcare organisations, exploiting vulnerabilities in networks to disrupt critical services and compromise patient data. In the Middle East, where digital adoption is accelerating, healthcare organisations must develop robust incident response plans that can swiftly address ransomware incidents. This requires not only strong cybersecurity protocols but also a culture of preparedness, with all staff trained to recognise and respond to ransomware threats early.
A proactive approach to ransomware defence goes beyond traditional security measures. Organisations must focus on network monitoring and threat detection to spot unusual activity that could signal an impending attack. Building resilience against ransomware means anticipating potential threats and establishing strategies to mitigate their impact before they escalate.
- How Are We Protecting Sensitive Patient Data?
Patient data is one of the most valuable targets for cybercriminals, making its protection a top priority. As the cost of data breaches continues to rise, healthcare organisations in the Middle East must implement comprehensive data protection strategies. This includes encryption, continuous monitoring, and adopting zero-trust architectures, where no one inside or outside the organisation is trusted by default.
Data protection is not only about securing information from external threats but also about ensuring that all users, including healthcare workers, follow best practices for data handling. Regular training and awareness programmes are essential to ensure that all staff members understand the importance of patient data security and how to avoid accidental breaches.
- How Can We Ensure Network Resilience?
Network resilience is critical in healthcare, where the ability to access patient records, deliver medical treatments, and maintain day-to-day operations depends on network availability. Downtime due to cyberattacks can have life-threatening consequences. As cyber threats grow more sophisticated, healthcare organisations must take steps to ensure that their networks are resilient in the face of potential attacks.
Building network resilience requires comprehensive visibility into network activity to detect anomalies in real time. By monitoring network traffic, organisations can identify and respond to threats quickly, minimising the impact of any disruptions. Implementing disaster recovery and business continuity plans is also essential to ensure that healthcare providers can continue to deliver care, even in the event of a cyber incident.
- Are We Complying with Cybersecurity Regulations?
Governments in the Middle East are increasingly implementing strict cybersecurity regulations to protect critical sectors like healthcare. Compliance with these regulations is essential to safeguarding patient data and ensuring the integrity of healthcare networks. Non-compliance can result in hefty fines, reputational damage, and the erosion of patient trust.
Healthcare organisations must stay informed about the regulatory landscape and ensure that they meet all relevant cybersecurity requirements. This includes regulations that govern data protection, breach notification, and the overall security of healthcare IT systems. Regular audits and the adoption of compliance automation tools can help streamline the process of ensuring that organisations are meeting these stringent requirements.
- Is Our Workforce Equipped to Handle Cyber Threats?
Human error remains one of the weakest links in cybersecurity, particularly in healthcare, where staff may inadvertently expose sensitive data. Ensuring that employees are equipped to handle cyber threats is crucial in building a resilient security culture. Training healthcare workers to recognise phishing attempts, follow secure data-handling procedures, and respond effectively to cybersecurity incidents is essential to minimising risks.
An informed workforce is a powerful defence against cyberattacks. Organisations should invest in continuous cybersecurity education, making sure that all staff members, from clinical personnel to administrative staff, understand the role they play in safeguarding patient data and the organisation’s IT infrastructure.
Conclusion
As the healthcare sector in the Middle East continues to embrace digital transformation, it also faces an increasingly complex and dangerous cybersecurity landscape. Addressing these five critical questions will help healthcare organisations better protect patient data, ensure operational continuity, and minimise reputational damage in the face of rising cyber threats.
By taking a proactive and strategic approach to cybersecurity, healthcare providers can not only defend against cyberattacks but also ensure the highest standard of care for patients in a digitally connected world.
Tech Features
THE CONVERGENCE OF CRISIS: HOW OVERLAPPING RISKS ARE REDEFINING WORKFORCE MOBILITY IN THE MIDDLE EAST

By Gillan McNay, Security Director Assistance – Middle East, International SOS
In today’s Middle East operating environment, mobility risk no longer arrives in isolation. Organisations are increasingly navigating multiple, overlapping disruptions that converge to affect how, when, and whether their people can move. Geopolitical tension, aviation restrictions, cyber exposure, misinformation, and workforce anxiety are no longer separate risk categories – they interact, amplify one another, and challenge traditional mobility assumptions.
This convergence is redefining what “safe movement” looks like for organisations with employees traveling, deployed, or working abroad across the region.
From Single Events to Layered Disruption
Historically, mobility planning focused on discrete scenarios, weather events, isolated security incidents, or airline strikes. Today, organisations are far more likely to face layered disruption, where one event triggers a cascade of secondary impacts.
A regional security escalation may coincide with airspace closures. Airspace closures may lead to congestion at land borders. Border congestion increases stress for travelers, which in turn heightens reliance on digital communication channels, precisely when misinformation and cyber activity surge. Each layer compounds the next.
International SOS’ Risk Outlook 2026 highlights this shift clearly: risk is now systemic and interdependent, not episodic. For mobility teams, this means plans designed for one‑dimensional threats will be insufficient.
Mobility Is Now a Strategic Exposure
Movement of people has become a strategic risk vector rather than a logistical one. When employees cannot travel as planned, the impact extends beyond delayed meetings or project timelines. It affects:
- Business continuity
- Leadership visibility
- Employee confidence and wellbeing
- Regulatory and duty‑of‑care obligations
In the Middle East, this is especially pronounced due to the region’s role as a global aviation hub and its highly international workforce. When airspace is disrupted in one country, the effects ripple across neighbouring states almost immediately.
As a result, organisations must treat mobility decisions with the same scrutiny as other strategic risks, cybersecurity, financial exposure, or supply‑chain dependency.
The New Reality: Mobility Under Uncertainty
In recent months, we have seen how quickly mobility conditions can change. Routes that were viable in the morning may be restricted by evening. Neighbouring jurisdictions may adjust entry requirements or limit transit with little notice. Information may circulate rapidly on social media before it can be verified.
The most resilient organisations recognise that movement decisions must be conditions‑based, not schedule‑based. Rather than asking “Can we move people today?”, leaders need to ask:
- What conditions would make movement unsafe tomorrow?
- What alternatives exist if a primary route closes?
- Are we prepared to shift from air to land, or to stabilise in place?
This approach requires planning optionality into every mobility decision.
Overlapping Risks Demand Integrated Decision‑Making
The convergence of crisis exposes one of the most common organisational gaps: mobility decisions are often segmented across functions. Security looks at threat levels, HR considers employee impact, travel teams focus on bookings, and IT monitors communications. In a converging‑risk environment, this fragmentation increases risk.
Mobility decisions must be informed by integrated intelligence, security assessments, aviation updates, border conditions, medical considerations and workforce sentiment. When these views are aligned into a single operating picture, organisations can act faster and with greater confidence.
This integrated approach is increasingly reflected in board‑level discussions, as highlighted in the Risk Outlook 2026, where executive oversight of crisis preparedness and workforce risk continues to rise.
The Human Layer Cannot Be Separated From Mobility
Overlapping crises do not only disrupt routes; they disrupt people. Uncertainty around travel amplifies stress, particularly for expatriates with families, employees traveling alone, or teams operating far from home support networks.
From an assistance perspective, we see that anxiety itself becomes a risk multiplier. Tired, stressed travelers are more likely to make poor decisions, rushing to airports prematurely, acting on unverified information, or attempting unsafe routing alternatives.
Mobility strategies must therefore incorporate psychological safety alongside physical safety. Clear guidance, predictable communication, and reassurance that decisions are being reviewed continuously make a material difference to outcomes.
Why “Move” Is Not Always the Right Answer
One of the most important shifts organisations are making is recognising that relocation or evacuation is not always the safest or most effective response. In converging‑risk scenarios, moving people can expose them to new uncertainties if the destination environment changes.
Stability, supported by shelter‑in‑place guidance, supply planning, and continuous monitoring, can be the safest posture while conditions clarify. Mobility planning should define three distinct postures:
- Stay and stabilise
- Relocate to a regional safe haven
- Evacuate out of the region
Each posture requires different triggers, communications, and support mechanisms. Treating them interchangeably increases risk.
Information Discipline Is a Mobility Imperative
Overlapping crises generate noise. For organisations managing mobility, information discipline becomes critical. Decisions based on rumours, unverified social media posts, or outdated aviation updates can lead to unnecessary movement, or unsafe delay.
Effective organisations establish clear information pathways:
- Who validates updates
- Which sources are trusted
- How frequently conditions are reviewed
- When decisions are escalated
This discipline supports faster pivots when conditions change and reduces the emotional load on traveling employees.
Building Adaptive Mobility for the Future
The convergence of crisis in the Middle East is not a temporary phenomenon. Geopolitical volatility, climate stress, digital disruption, and workforce expectations will continue to intersect. Mobility strategies must evolve accordingly.
Resilient organisations are already adapting by:
- Embedding workforce visibility into core systems
- Designing mobility plans with multiple fail‑safe options
- Training leaders to make people‑first decisions under pressure
- Aligning crisis planning with broader enterprise risk management
As the Risk Outlook 2026 underscores, preparedness is no longer about predicting the next event, it’s about building the capacity to adapt when events collide.
A Redefined Measure of Readiness
In this new operating reality, mobility readiness is not measured by the ability to move people quickly, but by the ability to make calm, informed, and proportionate decisions as risks converge.
Organisations that understand this will be better positioned to protect their people, maintain operational stability, and navigate periods of regional tension with confidence rather than urgency. The convergence of crisis is challenging, but with the right structures, discipline, and integration, it is manageable.
Tech Features
SUPPORTING EMPLOYEES ABROAD OR RELOCATING AMID REGIONAL TENSIONS: A STRATEGIC ADVISORY FOR ORGANISATIONS

By Gillan McNay, Security Director Assistance – Middle East, International SOS
Periods of regional tension place organisations under intense pressure to protect their people while sustaining operations. For UAE‑based companies with employees working from abroad, traveling frequently, or facing potential relocation, uncertainty can escalate quickly. Routes change, borders tighten, information moves faster than it can be verified, and employees look to their organisation for clarity and reassurance. In this environment, support must be strategic, deliberate, and people‑first.
Shift From Reaction to Preparedness
The most resilient organisations are those that move beyond reacting to events and instead operate with a preparedness mindset. This starts with acknowledging that uncertainty is not an exception but a condition organisations must continuously manage. Strategy, therefore, should anticipate disruption and define how the organisation will respond before decisions are forced by urgency.
Preparedness does not mean planning for every possible outcome. It means establishing decision frameworks that allow leaders to act confidently as conditions evolve, whether that results in continued remote work, relocation to a safe haven, or shelter‑in‑place with enhanced support.
Establish Workforce Visibility as a Strategic Capability
Supporting employees abroad begins with accurate, real‑time visibility. Leaders must know where their people are, their travel status, and whether they are working remotely, stationed overseas, or in transit with dependents. Visibility should extend beyond employees to include contractors and accompanying family members where duty‑of‑care obligations apply.
This visibility is strategic because it underpins all subsequent decisions. Without it, organisations risk delayed responses, fragmented communication, and uneven support. With it, they can act proportionately, supporting those most exposed while avoiding unnecessary disruption for others.
Differentiate Between Relocation, Evacuation, and Stability
One of the most common strategic mistakes during regional tensions is treating all movement decisions as evacuations. In reality, organisations need three clearly defined postures:
- Stability: Supporting employees to remain where they are with guidance, wellbeing checks, and secure working arrangements.
- Relocation: Moving employees to a safer location, often within the region, as a preventive measure.
- Evacuation: Executing time‑bound movement out of an area due to elevated risk.
Clear definitions allow leaders to choose the least disruptive option that still protects people. Often, relocation or stability with structured support is safer and more sustainable than rapid evacuation.
Prepare Employees Before Movement Is Required
Relocation becomes significantly smoother when employees are prepared before they are asked to move. Strategy should include guidance on documentation readiness, passport validity, visa requirements for neighbouring countries, preferred relocation countries and expectations around timelines and flexibility.
Employees working abroad need to understand not only what may happen, but how decisions will be made. When organisations explain decision triggers, what would prompt relocation, what would not, employees feel informed rather than anxious. This transparency builds trust and reduces panic-driven movement.
Integrate the Human Dimension into Planning
Strategic support must address the human impact of uncertainty. Employees working from abroad or facing relocation are often balancing professional obligations with family concerns, schooling, medical needs, and other emotional strains. Ignoring these factors weakens any relocation or stability strategy.
Effective organisations integrate wellbeing considerations into operational plans. This includes access to medical advice, continuity of prescriptions, support for family travel, and regular wellbeing check‑ins. Leaders should be attuned to signs of fatigue or anxiety and equip managers with guidance to support teams compassionately and consistently.
Communicate With Discipline and Predictability
In uncertain times, communication is as important as movement planning. Strategy should define how, when, and by whom information is shared. Centralised, fact‑based updates delivered at a predictable cadence reduce speculation and rumor.
Employees should know where official updates will come from and which sources to trust. Communications do not need to be frequent to be effective; they need to be consistent, clear, and grounded in verified information. Saying “there is no update yet” is often more reassuring than silence.
Support Employees Who Must Remain Abroad
Not all employees can or should relocate. Many will continue working from abroad in environments affected by regional tension. Supporting these employees strategically means ensuring they have guidance on local conditions, access to support services, and clearly defined expectations around work, availability, and safety.
Stability should be treated as an active posture, not inaction. Regular check‑ins, updated guidance, and contingency planning signal to employees that their situation is being managed deliberately, not overlooked.
Plan for Relocation as a Managed Process
When relocation is required and viable, it should be executed as a controlled, end‑to‑end process. This includes manifesting all individuals, front‑loading documentation checks, coordinating transport and accommodation, and communicating each step of the journey.
Strategically, leaders must also consider what comes after relocation: access to work, schooling for children, healthcare, and communication continuity. Relocation is not just movement; it is a temporary operating model that must be sustainable.
Learn, Adapt, and Strengthen
Each period of disruption provides insight into what worked and what did not. Strategic organisations capture these lessons and feed them back into planning. This may involve refining decision thresholds, improving data accuracy, or strengthening manager training.
Preparedness evolves as operating environments change, and organisations that invest in continuous improvement are better positioned to protect both their people and their business.
A Strategy Built on Trust and Clarity
Ultimately, supporting employees abroad or relocating amid regional tensions is a test of organisational maturity. Clear visibility, disciplined planning, transparent communication, and genuine care form the foundation of resilience. When organisations operate from these principles, employees feel supported rather than vulnerable, and leaders can make decisions with confidence rather than urgency.
Tech Features
IN THE AGE OF AI, THE BEST HEALTHCARE WILL STILL BE HUMAN

By Dr. Craig Cook, CEO, The Brain & Performance Centre, A DP World Company
Healthcare is entering one of the most transformative periods in its history. Artificial intelligence is accelerating diagnostics, enhancing imaging, and enabling more personalised treatment pathways than ever before. These advancements are no longer theoretical, they are already shaping how care is delivered across leading medical systems.
However, as the industry moves forward at pace, there is a risk of focusing too heavily on what technology can do, and not enough on what individuals actually need.
At its core, healthcare is not a technical transaction. It is a human experience. Within that experience, trust, communication and empathy are not optional, they are fundamental.
Strong human interaction between clinicians and clients remains one of the most important factors in delivering safe and effective care. Technology can identify patterns, process data and support decision-making, but it cannot replace the reassurance an individual feels when they are heard, understood and taken seriously. That interaction often determines whether someone follows through with treatment, shares critical information, or seeks support early rather than late.
From a safety perspective, this is critical. Individuals who feel comfortable with their clinician are far more likely to communicate openly about symptoms, concerns and uncertainties. They ask more questions, clarify instructions, and engage more actively in their own care. This level of engagement reduces the likelihood of miscommunication, improves adherence to treatment plans, and ultimately leads to better outcomes.
In contrast, when the human element is diminished, even the most advanced systems can fall short. An individual may receive accurate data but still leave uncertain about what it means. They may hesitate to disclose something important, or disengage entirely. No algorithm can compensate for that gap.
This is why meaningful communication must remain at the centre of healthcare delivery. It is not simply about explaining a diagnosis. It is about creating an environment where individuals feel safe to speak, where their concerns are acknowledged, and where complex information is translated into something clear and actionable.
As artificial intelligence continues to evolve, the role of the clinician will not diminish, it will become more important. Technology should reduce administrative burden, enhance precision, and create time. That time should be reinvested into the client relationship through greater clarity, deeper understanding and more considered care.
At The Brain & Performance Centre, A DP World Company, this balance is central to how we approach care. Advanced technologies play a critical role in our assessments and programmes, but they are always applied within a human-led framework. Every programme is personalised, every interaction is intentional, and every client journey is built on understanding the individual, not just the data.
The future of healthcare will undoubtedly be shaped by innovation. But its success will not be defined by how advanced the technology becomes. It will be defined by whether we use that technology to strengthen, rather than replace, the human connection at the centre of care. Because ultimately, the most powerful tool in healthcare is not artificial intelligence. It is trust.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR12 months ago
VAR12 months agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Trending5 months ago
Trending5 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 Tech Interviews2 years ago
Tech Interviews2 years agoNavigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Tech News9 months ago
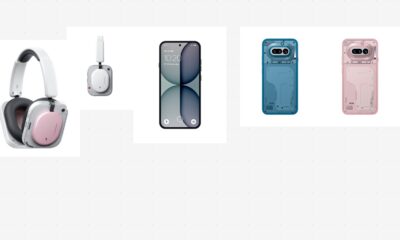
Tech News9 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive2 years ago
Automotive2 years agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms