Technology
Your Screen. Your Eyes Only: Galaxy S26’s Privacy Display Keeps Curious Eyes Away Without Blocking Your Experience

Samsung Electronics announced a landmark breakthrough in mobile hardware with the launch of the Galaxy S26 Ultra, featuring the world’s first built-in Privacy Display. While standard privacy solutions have traditionally relied on software or add-on films, Samsung is once again pioneering a new industry category by engineering visual protection directly into the device’s pixel-level architecture
Representing a landmark shift in the mobile industry, the Galaxy S26 Ultra delivers a permanent solution to a universal problem: the need for flexible privacy without compromise. By introducing world-first Privacy Display technology directly into the Galaxy S26 hardware, Samsung is transforming privacy from an optional accessory into an integrated standard of engineered trust.
Privacy When You Need it
In an era of high-density living, where mobile users skip between crowded elevators and public transport networks to busy cafes and gyms, the risk of “visual hacking” is higher than ever. Whether entering a banking PIN, drafting a confidential work email, or viewing private photos, the Galaxy S26 Ultra ensures the user’s content remains their eyes only, all the time.
Samsung’s Privacy Display utilizes a precision ‘Black Matrix’ structure to manage light travel at the pixel level. This hardware-first approach provides comprehensive 4-way protection: covering the left, right, top, and bottom angles. This ensures that your screen remains crystal clear from the front while fading into privacy for onlookers. Critically, because the technology is embedded in the display architecture, this protection stays perfectly in place even when the phone is rotated for horizontal viewing.
The “Techie” Verdict: A Breakthrough for Everyday Use
Tech experts have highlighted how this integrated protection solves real-world challenges:
Privacy For Every Situation
The Galaxy S26 Ultra’s world-first Privacy Display is designed to fit the rhythm of a busy day without adding friction to the user experience:
- Discretion on a Crowded Commute: Whether on a packed Metro, squeezed into a stacked elevator, switching to Maximum Privacy Protection ensures that even in tight quarters, the person next to you sees only a dark screen, while your content remains crystal clear.
- Automatic Security for Banking: You can set the display to activate automatically the moment you open a banking app or reach the lock screen, providing instant peace of mind in busy cafes or public squares. You have control over when and how the Privacy Display kicks in.
- Vibrant Quality for Shared Moments: Unlike add-on gadgets or display films that dull images, this pixel-level protection maintains rich colors and sharp details. It remains active even in landscape mode, allowing you to show a friend a video while keeping side-viewers at bay.
A New Standard for Mobile Security
The Galaxy S26 Ultra is the first device to recognize that mobile security is no longer a luxury, it is a need in every phone. By switching to a hardware-backed foundation of security, the Samsung S26 redefines what it means to be secure. Samsung is once again redefining what technology can be.
Tech News
TALLY SOLUTIONS RECOGNISED BY UAE MINISTRY OF FINANCE AS A PRE-APPROVED E-INVOICING SERVICE PROVIDER

Tally Solutions, a leading global technology company providing business management software to small and medium businesses worldwide, has been included in the UAE Ministry of Finance’s list of Pre-Approved E-Invoicing Service Providers under the country’s upcoming e-invoicing framework.
With this recognition, Tally further strengthens its position as one of the most trusted and relevant business management solutions for SMEs in the UAE. As one of the few globally established providers with a strong SME focus to achieve this status, Tally is well placed to help businesses transition confidently to the next phase of digital compliance.
The inclusion reflects Tally’s long-standing approach of combining simplicity, localisation, and regulatory readiness into everyday business workflows. For SMEs, where time, cost, and ease of adoption are critical, the move to e-invoicing requires more than technical compliance; it requires a solution that is dependable, intuitive, and built around real business needs.
Over the years, Tally has supported businesses across multiple markets through major regulatory transitions, including VAT implementation, e-invoicing mandates, and digital tax reforms. In the UAE, this experience is complemented by continued investments in bilingual capabilities, connected compliance features, secure cloud-enabled access, and product innovations that help businesses remain future-ready without added complexity.
Commenting on the announcement, Vikas Panchal, General Manager – MENA, Tally Solutions, said: “At Tally, our purpose has always been to empower SMEs with technology that is simple to adopt, reliable to run, and easy to scale. Being recognised as a Pre-Approved E-Invoicing Service Provider by the UAE Ministry of Finance is an important milestone and a reflection of the trust we have built with businesses across the region. Having supported regulatory transitions in multiple markets, we understand that compliance must be practical, not complicated. Our focus is to ensure UAE businesses can embrace e-invoicing with confidence while continuing to grow without disruption.”
The recognition also comes at a time when the UAE’s e-invoicing market is witnessing strong momentum, driven by the country’s broader digital economy agenda and the growing adoption of structured financial systems. As businesses prepare for this shift, Tally’s pre-approved status gives SMEs the confidence of choosing a solution already aligned with the government’s evolving framework.
Currently, around 20 companies have been listed by the Ministry of Finance as pre-approved e-invoicing service providers. While many providers in the accounting and ERP segment primarily cater to large enterprises, Tally continues to stand apart through its strong focus on SMEs, delivering compliant, accessible, and scalable solutions designed for the realities of growing businesses.
Tech Interviews
The Next Horizon: Manish Bakshi on BenQ’s Vision for a Human-Centric Digital Decade

An exclusive conversation on AI ecosystems, smart learning and how modern leadership paradigms are redefining agility and long-term business resilience
As he marks nearly 25 years with BenQ Middle East, Managing Director Manish Bakshi looks firmly ahead, sharing his vision for the next decade of AI-powered ecosystems, smart learning, hybrid collaboration, esports and immersive home entertainment. In this exclusive Q&A, he discusses how BenQ is preparing to lead the next phase of digital transformation in the region.
After nearly 25 years of building BenQ in the region, what excites you most about the next decade?
Manish Bakshi: What excites me most is that we are moving beyond individual devices into connected, intelligent ecosystems. The next decade will not simply be about better hardware; it will be about how technology works together seamlessly to make experiences more intuitive, productive and human-centric.
At BenQ, we see the future being shaped by AI-powered ecosystems across education, enterprise and consumer technology. Whether it’s smart classrooms, intelligent meeting spaces or immersive home entertainment, our focus is on enabling technology that feels almost invisible, powerful, but effortless to use.
The Middle East is a particularly exciting region for this evolution because of the pace of digital transformation and the ambition we see across sectors.
You often speak about moving from products to ecosystems. What does that mean in practical terms?
Manish Bakshi: Traditionally, technology companies focused on standalone products. Today, the real opportunity lies in ecosystems, where displays, software, collaboration tools, cloud services and AI work in harmony.
For us, innovation is increasingly about creating connected solutions rather than isolated devices. In a meeting room, for example, the display, conferencing tools, wireless presentation systems and collaboration software should operate as one seamless environment.
AI will take this further by making those ecosystems adaptive, learning user preferences, simplifying workflows and enabling smarter decision-making.
That is where we see the future of technology heading.
Education is evolving rapidly. How do you see smart classrooms developing over the next five to ten years?
Manish Bakshi: We believe classrooms will become far more intelligent and personalised. The future is not just digital whiteboards replacing traditional ones, it’s AI-enabled learning environments where technology adapts to students’ needs in real time, provides teachers with actionable insights and makes learning more interactive and inclusive.
In the Middle East, governments and institutions are investing heavily in education transformation, and we see strong momentum around smart learning.
BenQ intends to play a leading role in this space by developing solutions that combine interactive displays, software ecosystems and well-being-focused innovation, including technologies designed around eye care and healthier learning environments.
The goal is simple: technology should support better learning outcomes, not add complexity.
Hybrid work has matured significantly. What’s the next chapter for workplace innovation?
Manish Bakshi: The first phase of hybrid work was about enabling remote participation. The next phase is about optimising the experience.
The future workplace will be frictionless. You walk into a meeting room, your device connects instantly, the room recognises your preferences, collaboration starts without delays, everything just works. We’re focused on intelligent meeting ecosystems that make collaboration natural regardless of location.
Another major focus will be human-centric workplace design, ergonomic displays, wellness-driven technologies and environments designed for long-term productivity and comfort.
The future office is not only smarter; it has to be healthier.
AI is driving much of today’s innovation conversation. How do you see AI transforming BenQ’s categories?
Manish Bakshi: AI will become the intelligence layer across everything we do. In education, it will personalise learning. In an enterprise, it will streamline collaboration and improve productivity. In consumer technology, it will create richer, more intuitive experiences.
But importantly, we see AI as an enabler, not a replacement for people. The role of AI is to remove friction, simplify complexity and empower users. That human-centric approach is very important to us.
Esports and gaming have become major growth sectors in the region. How do you view this opportunity?
Manish Bakshi: Esports is no longer niche; it is a mainstream ecosystem with economic, cultural and technological significance. The Middle East has made remarkable investments in gaming infrastructure, tournaments and talent development, and we see enormous long-term potential.
Our vision is not only to support professional esports through high-performance gaming innovation, but also to contribute to the growth of grassroots gaming communities in the region. This sector represents the convergence of technology, youth culture and digital creativity, and it will continue to expand.
BenQ has also been expanding into home entertainment. What trends do you see shaping that space?
Manish Bakshi: The home is being reimagined as an immersive entertainment space. Particularly in the GCC, where home experiences and family gatherings are such an important part of culture, we are seeing strong interest in cinematic home technologies. Laser TVs and ultra-short-throw projectors are transforming how people think about entertainment at home.
We see significant growth in this category over the coming years and plan to continue expanding solutions designed for the unique lifestyle and architectural preferences of the region.
This is one of the most exciting consumer opportunities ahead.
How do you see BenQ Middle East contributing to the region’s wider digital transformation agenda?
Manish Bakshi: Our role is to be more than a technology provider; we want to be a transformation partner. Across education, corporate and consumer segments, our focus is on supporting the region’s ambitions through innovation that aligns with future needs. That includes smarter ecosystems, sustainability-driven design, AI-enabled solutions and technologies that improve both productivity and well-being.
The Middle East is not just adopting innovation; in many areas, it is helping define it. We want to be part of shaping that future.
What leadership principle will guide you into this next decade?
Manish Bakshi: One principle remains constant: technology must serve people. No matter how advanced innovation becomes, the human element stays central. Leadership today is increasingly about orchestration, bringing together people, ideas and technology to create value collectively.
The next decade will belong to organisations that combine intelligence with purpose. For us at BenQ, the future is not simply about building smarter technologies. It is about enabling smarter, more meaningful experiences. And that is the vision driving our next chapter.
Tech Features
Why AI Transformation is a Human Imperative, and the Role the CHRO Must Play

A year after IBM’s Deep Blue defeated Garry Kasparov in 1997, Kasparov did something unexpected. Rather than retreat, he invented a new form of chess he called ‘advanced chess’, pairing human players with computers to see what they could produce together. The result was remarkable. Even moderately skilled players, armed with a standard machine, were capable of defeating both grandmasters playing alone and computers operating without human input. The combination was categorically superior to either element in isolation.
By: David Henderson , Group CHRO, Al-Futtaim
That experiment carries an important lesson for organisations navigating AI today. The instinct understandable, but mistaken, is to frame AI as a technology story. It is not. AI reshapes jobs, redistributes decision rights, resets operating models, and forces us to reconsider deeply embedded ways of working. It intersects directly with creativity, cognition, confidence, identity and employability. It produces as many human questions as it does technical ones.
This is why the organizations that are genuinely converting AI from experiment into competitive advantage are those that have understood it, first and foremost, as a large-scale human transformation, one that demands the business, the CHRO and the CIO working as genuine partners, each bringing what the other cannot.
The organisations winning with AI are not those with the most sophisticated technology. They are those that have most deliberately redesigned how humans and machines work together.
The Case for the CHRO
The most effective AI transformations are driven by a tight three-way partnership:
the business setting the agenda and owning outcomes,
the CIO providing the technology platforms,
data infrastructure and governance,
and the CHRO leading the human transformation that determines whether AI delivers value at scale or stalls in pilots.
Each is essential. None is sufficient alone.
What has changed is the recognition that the human dimension, the design of work and decision rights, the building of workforce capability, the management of trust and ethics, the orchestration of adoption across large and diverse employee populations, is not downstream of the technology. It is a primary enabler of it. That is the CHRO’s territory, and it demands the same strategic weight as the technology agenda itself.
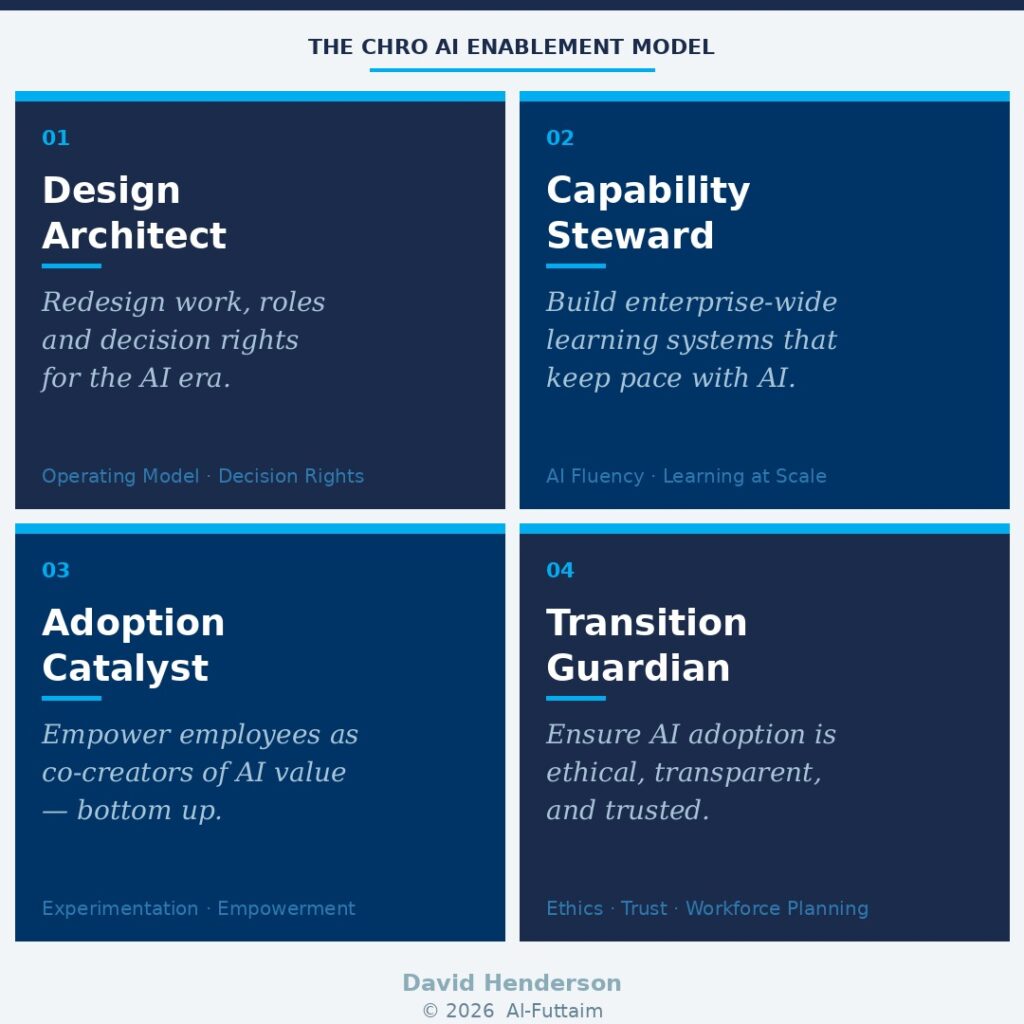
In this paper, I propose a model for how CHROs can lead AI enablement through four interconnected roles: Design Architect, Capability Steward, Adoption Catalyst, and Transition Guardian. Each role addresses a distinct dimension of the human transformation that AI demands. Together, they represent a holistic operating mandate for CHROs who are serious about delivering sustained enterprise value from AI, not just deploying tools.
01) Design Architect: Redesigning work, roles and decision rights for the AI era
AI transformation fails far more often because of organisational design choices than because of technology limitations. When companies deploy AI tools without redesigning how work is done, decision rights blur, accountability erodes, adoption stalls, and productivity gains remain trapped in pilots. The technology is rarely the binding constraint. The organisation almost always is.
The CHRO’s role as Design Architect is to get ahead of that problem. This means providing overarching direction on how work should be redesigned so that human judgment and AI-generated insight are deliberately combined, not accidentally layered on top of each other. It means clarifying which decisions remain human-led, which are AI-supported, and where accountability ultimately sits. And it means building an operating model architecture that is dynamic enough to evolve as AI capabilities continue to develop rapidly.
In my own experience, incrementalism in this domain is almost always destined to fail. The organisations that are getting this right are making bold, decisive design choices, and in some cases, breaking up parts of the organisation that have long been treated as untouchable.
| In Practice — Procter & Gamble P&G redesigned decision models across forecasting, procurement and product innovation so that AI produces insights and options while humans retain final say on portfolio bets, supplier strategy and innovation priorities. Critically, AI was embedded directly into logistics decision forums — rather than remaining siloed in group-level analytics teams, removing information-sharing barriers and enabling real-time decision-making at scale. |
In Practice — Microsoft Microsoft intentionally redesigned all knowledge-work roles so that AI copilots handle drafting, synthesis and retrieval, while employees retain judgment, prioritisation and accountability. The result was not simply cost reduction,it was the redeployment of released cognitive capacity into revenue-generating innovation and customer experience improvement. |
Being intentional on organisational design means staying one step ahead of technological adoption, not one step behind it. The CHRO must proactively reimagine how AI reshapes the value chain and translate that vision into operating model decisions — rather than reactively course-correcting after tools have already been deployed.
02) Capability Steward: Building enterprise-wide, continuous learning systems that keep pace with AI
In the AI era, capability, not technology, is the primary constraint on value creation. The organisations that are scaling AI effectively are not those with the most sophisticated tools. They are those whose people know how to use them confidently, critically, and productively in the context of real work.
The CHRO’s role as Capability Steward is to build the learning infrastructure that makes this possible at scale. This means moving decisively away from episodic, one-size-fits-all training models, which are structurally unsuited to the pace of AI change, towards continuous, contextual learning systems that are embedded in daily workflows.
It means developing AI fluency across the workforce, not just in specialist teams. And it means maintaining ongoing insight into which capabilities are emerging, shifting or declining as the skills economy evolves.
| In Practice — Amazon Amazon treats AI capability as core workforce infrastructure rather than a specialist skill. It has built role-specific learning pathways combining foundational AI fluency with immediate, in-role application, particularly in operations, logistics and corporate functions. The result has been faster adoption of AI tools across large frontline and corporate populations, with measurable productivity gains driven by applied capability rather than isolated expertise. |
| From My Experience — Zurich Insurance During my time at Zurich, we built an enterprise-wide AI and digital capability ecosystem that combined broad AI literacy with deep domain-specific learning for underwriters, claims handlers and risk professionals. Learning was continuous and embedded in daily workflows. Critically, we also focused on transferable skill identification, enabling us, for example, to rapidly retrain and redeploy claims handlers as customer service agents based on strong overlaps in their underlying skill profiles. That flexibility became a genuine competitive asset. |
The CHRO must protect long-term capability health and resilience, not simply optimise for short-term productivity. Organisations that treat AI learning as a one-time training event will struggle to sustain adoption. Those that build continuous learning as an organisational capability will compound their advantage over time.
03) Adoption Catalyst: Empowering employees as co-creators of AI value, not passive recipients of it
Many CHROs of my generation were trained in a change management orthodoxy that starts at the top of the house, guiding coalition, executive sponsorship, structured project timelines. That model is not wrong, but it is increasingly insufficient for AI.
Top-down governance and strategy remain essential. But scalable AI value does not come from mandates. It comes from the bottom up, from employees who understand the work and are empowered to apply AI where insight is deepest and value most immediate.
The CHRO’s role as Adoption Catalyst is to create the conditions for this to happen: building cultures of experimentation and knowledge-sharing, aligning incentives and recognition to reward participation, and enabling employees to co-create AI use cases rather than simply receive them.
This is a fundamental shift from change management to what I would call change orchestration, leaders creating the environment in which adoption flourishes, rather than driving it through compliance.
| In Practice — Al-Futtaim Blue Loyalty Platform The clearest proof point I can offer comes from our own experience at Al-Futtaim. The group’s Blue Loyalty Platform uses AI to combine behavioural, transactional and partner data to deliver personalised offers and purchase recommendations across our retail and service channels. What made this work was not central design — it was that the use cases were developed by multi-disciplinary frontline retail employees, working in agile action-learning teams, applying their direct customer insight to build the recommendations. AI was embedded into frontline and digital workflows by the people who understood those workflows best. The result has been measurable revenue uplift driven by use cases rooted in real customer interactions — not boardroom hypotheses. |
| In Practice — Google Google runs AI adoption through a culture of experimentation supported by internal communities, shared tooling and lightweight governance. Employees apply AI to improve workflows, products and services; successful use cases are productised and scaled through internal platforms. This produces rapid diffusion of best practices, strong employee ownership, and continuous improvement generated by those doing the work. |
Employees need to define the tools they need , not simply learn the tools they are given. That distinction is everything when it comes to whether AI adoption takes root or stalls.
Bottom-up adoption is not a cultural nicety. It is the mechanism through which AI becomes embedded, differentiated and commercially meaningful at scale. Organisations that get this right do not deploy AI. They make AI part of how the organisation thinks.
04) Transition Guardian: Ensuring AI adoption is ethical, transparent, and in the long-term interest of employees
AI introduces legitimate concerns that the CHRO cannot afford to minimise: fairness, transparency, surveillance, bias, job security, long-term employability. If these concerns are not addressed proactively and honestly, trust erodes, and without trust, adoption stalls regardless of how good the technology is.
The CHRO’s role as Transition Guardian is to ensure that AI adoption is consistent with organisational values and strengthens, rather than undermines, the employee value proposition.
This means embedding ethical guardrails and human oversight into AI adoption from the outset, not retrofitting them under regulatory pressure. It means communicating honestly with employees about what AI will change, what it will not change, and what pathways exist for reskilling and redeployment.
And it means treating strategic workforce planning not as an HR administrative function, but as a core enabler of organisational resilience.
Today’s employees need to focus less on specific target jobs and more on building transferable skill profiles that will serve them across a career that is certain to be turbulent. They need to feel that their organisation has their back. The CHRO must make that commitment credible, not through reassurance, but through concrete pathways.
| In Practice — Salesforce Salesforce has embedded ethical and responsible AI as a prerequisite for scale rather than a control imposed after deployment. The company requires mandatory Responsible AI training, applies humanin-the-loop oversight for AI-enabled decisions, and maintains clear disclosure standards when AI influences employee or customer outcomes. The trust this generates has driven faster adoption, stronger employee engagement, and meaningfully reduced legal, regulatory and reputational risk. |
| In Practice — Unilever Unilever explicitly links AI adoption to employability and internal mobility. As AI reshapes roles, the company invests heavily in reskilling and redeployment pathways, reframing AI as augmentation rather than displacement. Workforce planning, learning and ethics are intentionally connected rather than siloed , and employees can see a credible future for themselves within the transformation. |
Trust is not a soft outcome of AI transformation. It is the hard prerequisite for scaling it. The CHRO who treats it as such will find that ethical, transparent AI adoption does not slow the transformation down — it is the thing that makes it durable.
The CHRO Skill set for AI Enablement
Having defined the four roles the CHRO must play, it is worth being specific about the skills and attributes required to execute each one. In an environment where AI success is increasingly determined by organisational design, capability building, adoption dynamics and trust, not technology, these capabilities define whether the CHRO is shaping the transformation or reacting to it.
| Design Architect | Capability Steward | Adoption Catalyst | Transition Guardian |
| Operating Model Design | Learning at Scale | Change Orchestration | Ethical Judgement |
| Work & Role Deconstruction | AI Fluency Translation | Employee Empowerment Mindset | Trust Stewardship |
| Decision Rights Clarity | Skills Architecture & Workforce Sensing | Incentive & Recognition Design | Strategic Workforce Planning |
| Systems Thinking | Action Learning Systems | Business Experimentation Literacy | Risk Anticipation |
| Enterprise Co-Creation | Future Capability Stewardship | Cultural Signal Awareness | Clear, Honest Communication |
A few points of emphasis.
As Design Architect, the most underrated skill is enterprise co-creation — the confidence and credibility to act as a genuine co-owner of AI strategy with the CIO and business leaders, not merely as a supporting function.
As Capability Steward, future capability stewardship is distinct from short-term productivity optimization; CHROs must protect long-term organisational resilience, not just near-term performance.
As Adoption Catalyst, cultural signal awareness is often more powerful than formal programmes, leadership language and behaviour either accelerate or silently undermine adoption at scale. And as Transition Guardian, clear and honest communication, including on uncertainty and difficult tradeoffs, is the foundation on which all of the other skills rest.
Without it, none of the others land.
Conclusion: The Human Transformation Imperative
Organisations that are genuinely winning with AI are not those with the most sophisticated technology stacks. They are those that have most deliberately and thoughtfully redesigned how humans and machines work together, rethinking operating models, building capability at scale, empowering employees as co-creators, and managing the transition with ethics and transparency.
The CHRO who grasps this, who acts as Design Architect, Capability Steward, Adoption Catalyst and Transition Guardian simultaneously, becomes one of the most important executives in the organisation. Not because HR has staked a claim to a technology agenda, but because the most important levers for AI value creation are organisational and human, and those are precisely the levers that CHROs are equipped to pull.
Kasparov’s advanced chess experiment showed us, a quarter of a century ago, that the most powerful outcomes emerge not from humans or machines working alone, but from their deliberate, skillful combination. The CHRO’s mandate is to make that combination work, at enterprise scale, at pace, and without losing the trust of the people it depends on.
That is not a supporting role. It is a defining one.
_______________________________________________________
David Henderson is Group CHRO of Al-Futtaim Group, one of the Middle East's largest diversified conglomerates. He has previously served as CHRO of Zurich Insurance Group, MetLife and PepsiCo.

-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 Trending6 months ago
Trending6 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 VAR1 year ago
VAR1 year agoMicrosoft Launches New Surface Copilot+ PCs for Business
-
Tech Interviews2 years ago
Navigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Tech News10 months ago
Tech News10 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive2 years ago
Automotive2 years agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms












