Tech News
RACE Model: Building Cyber Resiliency and Mitigating Network Risks by Going Back to Basics

By H.E. Dr. Mohamad Al Kuwaiti, Head of Cybersecurity, UAE Government, and Dr. Aloysius Cheang, Chief Security Officer, Huawei Middle East & Central Asia

Jim Rohn once famously said, “Without a sense of urgency, desire loses its value.” Resilience is key to surviving in today’s world full of emerging technologies and hot-button buzzwords. It is a race towards all that is good, towards cyber survivability, a race of the utmost urgency and importance. As such, cybersecurity and, in particular, cyber resiliency is more than just having an incident response plan or a computer security policy. It is about ensuring that your entire security posture can withstand a wide range of threats, which includes hybrid, blended attack vectors that can transcend time and space through the interplay of physical, cyber, and virtual planes that take apart traditional brick-and-mortar aspects of any organizations and cross-borders jurisdiction.
Hence, we need to design a more holistic security framework by integrating cyber and physical security measures, hardening critical systems, and creating cross-functional teams and multi-disciplinary teams that will involve team members not only from our own organization but also from other stakeholders in our ecosystem that can address risks from multiple angles. Indeed, designing an auto-adaptable, self-evolving security framework that will evolve alongside the volatile and rapidly evolving threat landscape will be crucial to maintaining cyber resiliency and, therefore, safeguarding the business in the new intelligent era. But, without a doubt, there’s an urgent need to prioritize building cyber resiliency above all other matters.
Leonardo Da Vinci said, “I have been impressed with the urgency of doing. Knowing is not enough. We must apply. Being willing is not enough. We must do.” To build resilience, having a lofty mission statement with an ambitious plan is definitely not enough; the efforts must be grounded in the practicality of getting our hands dirty and being able to paddle in and out of the mudflats regardless of how much the mud will engulf you.
Figure 1 shows our proposed RACE model as a simple four-part process to look at how organizations can build cyber-resiliency with a feasible and actionable plan to achieve our objective of securing any organization by going back to basics. By going back to basics and doing them well, it will at least address 90% of the problems that most organizations are facing today. The solution needs not to be complex nor flamboyant; it just needs to be practical, and if one can cut through the levels of complexity and zero in on the crux of the problem and put in place basic security controls that are effective and efficient, it will lay the groundwork for success.
Borrowing the analogy of racing, would you be driving a race car that has a manual gearbox for full control and is tuned for the race track, or would you just take any car straight from the garage untuned for the conditions of the race track and relying on the car’s automatic gearbox to take care of the driving? Thus, it is clear that returning to basics and tuning your security measures for accuracy and precision is a much better bet than pouring huge investments into advanced systems and mechanics, building layers and layers of security indiscriminately.
Being accurate and precise will enable us to build quantifiability into our cybersecurity program. Accuracy and precision are both ways to measure results. Accuracy measures how close results are to the true or known value, while precision, on the other hand, measures how close results are to one another or, in other words, how well our defenses are designed and executed. This is our motivation behind the development of the RACE model. The subsequent paragraph will describe each key component of the model in greater detail.

Figure 1: The RACE model, a simple 4-part plan for building cyber resilience
Firstly, resiliency in modern cybersecurity speaks to the capability to provide value for the customer. In simplistic terms, it is to provide robustness and survivability of the organization’s cyber footprint in the face of adversaries and threats, meet compliance needs for business governance while excelling and providing a competitive advantage, using whatever security capabilities are based on established best practices, processes, and frameworks that achieve repeatable results. Figure 2 below summarizes what it takes to build cyber resilience and the value it brings to the table, taking into consideration the interplay between being compliance and building capabilities to support the resiliency of the entire information infrastructure that supports the business of an organization.

Figure 2: Building trust, enhancing cyber resilience, and mitigating risks in action
Next, awareness refers not only to imbuing a culture of cybersecurity among all the staff in an organization to the extent that basic cyber hygiene can be practiced but also to targeting the team focusing on delivery and maintaining ICT and security services within the organization so that they pay attention to cementing their core competencies and fundamentals. Hereby, it is recommended that harnessing risks and hedging your bet against the barrage of threats based on a risk-based approach is the best way, given that resources on hand are always scarce, limited, and, to some extent, expensive. Given that is the case, we have identified five basic core fundamentals that every cybersecurity team in any organization needs to build up on their basics (and manage them well) based on common cybersecurity issues faced, as depicted in Figure 3. While it may seem simple, the devil is always in the details to ensure a job is done well.

Figure 3: Managing five common risks (end-to-end) comprehensively as a basis for building cyber resilience
One man, organization, or country cannot resolve cybersecurity issues alone. It takes an entire village to address cybersecurity issues as they affect everyone if anything goes awry. Cybersecurity is a team sport, and all the stakeholders within the ecosystem must contribute towards addressing the elephant in the room, as shown in Figure 4. We always find strength in numbers because “united we stand, divided we fall.” We see the Blackhat community is doing that exactly, and that is why they are always a step ahead of the good guys every time, thereby summarizing the urgency to Collaborate as a key differentiating measure.

Figure 4: Cybersecurity is a team sport. So, who is on the team?
Last but not least, we need to bring everything together to build or Engineer the process, putting the cogwheels into their rightful places to drive the engine forward. We have identified five key fundamental security measures that, if done diligently, will be key to building an end-to-end resilient system and reducing network risks.
As shown in Figure 3, the five key fundamental security measures are 1) software integrity protection, 2) security configuration, 3) digital certification management, 4) vulnerability remediation, and 5) product lifecycle management. Take “Security configuration” as an example. To engineer and address the risk brought about by system misconfiguration, we need to break it down into its elements or identify its Work Breakdown Structure or WBS, which is a key step for planning project tasks and allocating resources.

Figure 5: Security Configuration Example: Optimize the Security Configuration Baseline based on Service Scenarios
Figure 5 summarizes typical work done to break down “security configuration” into its WBS. While this figure does not depict the complete picture, it does show a deep dive into each piece of work. One should keep working on breaking it down until the project scope and all the tasks required to complete the project can be visualized in one snapshot.
In conclusion, we have distilled the entire RACE model in detail in this paper. Achieving RACE is key to building resiliency for any organization. The important thing to note is to keep it simple and go back to basics. Build an auto-evolving, adaptable security framework based on the strategy that is designed to shape-shift alongside emerging blended, hybrid threats by leveraging on actionable intelligence, building resilience, and fostering collaboration so that individuals, organizations, and nations. Establishing public-private partnerships (PPP) with governmental entities and authorities enables public sector players, such as the UAE Cyber Security Council, to act as the fulcrum for coordinating and pooling resources and intelligence. This will enable our modern society to defend against today’s threat and safeguard one’s digital journey by addressing the challenges of tomorrow’s Age of Intelligence.
Tech News
Intel Core Series 3 Extends AI-Ready Performance to Value and Edge Computing Segments

Intel has introduced its latest Intel Core Series 3 mobile processors, aimed at expanding advanced computing capabilities to value buyers, commercial users, and essential edge deployments.
The launch reflects a broader shift in the industry, where performance, efficiency, and AI readiness are no longer confined to premium systems but are increasingly expected across all tiers of computing.
Built on the architectural foundations of Intel’s newer Core platforms and leveraging advanced process technology, the Core Series 3 processors are designed to deliver a balanced combination of performance, battery efficiency, and scalability. The focus is on enabling reliable, everyday computing while supporting emerging workloads, including AI-driven applications.
Driving Value-Oriented Performance
Intel positions Core Series 3 as a significant upgrade path for users operating on older systems. Compared to five-year-old PCs, the new processors deliver up to 47% improvement in single-thread performance and up to 41% gains in multi-thread workloads. GPU-based AI performance also sees notable enhancements, enabling improved responsiveness in modern applications.
This performance uplift is complemented by a strong emphasis on efficiency, with reduced processor power consumption and optimisations aimed at extending battery life for mobile systems.
AI Capability Moves to the Mainstream
One of the key differentiators of the Core Series 3 platform is the introduction of hybrid AI-ready architecture within the value segment. With support for up to 40 platform TOPS, Intel is enabling a new class of systems capable of handling AI workloads at the device level.
The platform also integrates modern connectivity standards, including Thunderbolt 4, Wi-Fi 7, and Bluetooth 6, ensuring compatibility with next-generation peripherals and networks.
Expanding into Essential Edge Deployments
Beyond traditional laptops, Intel is positioning Core Series 3 as a scalable solution for edge computing environments. The processors are designed to support a wide range of applications, including robotics, smart buildings, retail systems, and industrial deployments.
By combining AI acceleration with energy efficiency, the platform aims to deliver the performance required for real-time processing while maintaining operational reliability in diverse environments.
Ecosystem and Availability
Intel expects broad adoption across the ecosystem, with more than 70 designs from OEM partners set to launch across multiple form factors. Consumer and commercial systems powered by Core Series 3 are rolling out through 2026, while edge-focused deployments are expected from Q2 onwards.
Tech News
62% OF SAUDI LEADERS ARE FAILING TO USE THEIR DATA EFFECTIVELY, NEW CLOUDERA REPORT FINDS

Cloudera, the only company bringing AI to data anywhere, today released its latest global survey, The Data Readiness Index: Understanding the Foundations for Successful AI, examining how prepared enterprises are to support AI at scale. Surveying more than 300 IT leaders in the EMEA region, including strong insights from Saudi Arabia, the report finds that while AI adoption is growing, most organizations still lack the data foundation needed for success.
The findings highlight a sharp contrast in how effectively organizations track their data. Nearly 9 in 10 EMEA IT leaders claim complete visibility into where all their data resides, compared to just 32% of respondents in Saudi Arabia. Furthermore, 62% of Saudi respondents cite data access restrictions as a major roadblock to effective data use.
This gap highlights an emerging ‘AI readiness illusion’: the belief that organizations are prepared to scale AI even as critical data challenges remain unresolved.
“Enterprises aren’t struggling to adopt AI, they’re struggling to operationalize it beyond experiments,” said Sergio Gago, Chief Technology Officer at Cloudera. “AI is only as effective as the data that fuels it. Without seamless access to all their data, organizations limit the accuracy, trust, and business value that AI can deliver. You can’t do AI without data.”
AI Adoption is High, but ROI Remains Elusive
While AI is now deeply embedded across the enterprise, achieving consistent returns on investment remains difficult due to a sharp geographical divide in implementation hurdles. Across EMEA, the struggle is largely centered on the inputs, with data quality issues (18%) and cost overruns (16%) cited as the primary causes of lackluster ROI. However, Saudi Arabia presents a different challenge focused on execution. In the Kingdom, weak integration into workflows is the overwhelming barrier at 29%, nearly doubling the concern over data quality, which sits at 15%.
These regional nuances are further tangled by significant infrastructure limitations. Around 65% of respondents in KSA report that performance constraints have hindered operational initiatives, highlighting the immense difficulty of scaling AI across fragmented environments.
Bridging The Data Gap
At the core of these challenges is a significant disconnect between data optimism and operational reality.
The report highlights that 95% of KSA respondents are highly confident in their data, but only 32% of that data is currently fully governed. While this outpaces the broader EMEA region, where only 26% of data is governed despite 91% confidence, it highlights a critical execution gap that organizations are now racing to fill.
The Kingdom is uniquely positioned to bridge this divide with 100% of Saudi respondents ready to adopt new governance frameworks, and 79% being extremely willing to transform their operations. This regional commitment suggests that Saudi Arabia’s proactive approach will likely outpace its peers in the race toward AI and digital maturity.
Strategic Alignment and the Accountability Gap
While leadership in both the EMEA and KSA regions understands the necessity of data infrastructure, the execution and accountability frameworks are worlds apart. More than 90% of EMEA respondents report a well-defined data strategy tied directly to business objectives, while only over half (53%) of Saudi Arabian respondents feel the same level of alignment.
Accountability and internal culture further widen this divide. In EMEA, 69% of leaders hold the CIO or CTO chiefly responsible for data readiness, whereas in Saudi Arabia, only 35% place ultimate responsibility on this role, indicating a more emerging ownership structure.
Beyond accountability and alignment, respondents in Saudi Arabia face a unique internal hurdle: 50% struggle with insufficient data literacy, while nearly a third (32%) cite a lack of executive sponsorship.
Data Readiness Will Define the Next Phase of Enterprise AI
As enterprise AI shifts from experimentation to execution, data readiness is emerging as the defining factor separating leaders from laggards.
Organizations able to fully access and govern all their data, wherever it resides, are far better equipped to deliver trusted, scalable AI. Notably, every respondent in the report indicated their organization is willing to adapt existing frameworks to support true data readiness.
As enterprises confront the limits of the AI readiness illusion, the path forward is clear: unlocking AI’s full value will require more than ambition; it will demand genuine data readiness. Those that close this gap will be best positioned to drive lasting impact and lead the next era of intelligent business.
Tech News
OPTRO LAUNCHES AI-POWERED GRC CAPABILITIES FOR THE MODERN ENTERPRISE WITH AI GOVERNANCE, CYBER RISK, AND CONTINUOUS CONTROL MONITORING

Optro, the leading AI-powered GRC platform empowering enterprises to transform risk into opportunity, has announced several product capabilities to boost the effectiveness of customers’ risk management programs and enable them to innovate with AI confidently and responsibly. These capabilities follow shortly after the company changed its name to reflect what its AI-powered GRC platform enables: a single, coherent view across infosec, compliance, risk, and audit.
“Cyber risk now moves at machine speed, and legacy GRC tools can no longer keep up,” said Happy Wang, Chief Product and Technology Officer at Optro. “By leveraging AI to predict cyber risk, surface real-time insights, and accelerate mitigation, we help organizations shift from reactive reporting to proactive risk defense—building a true system of action that is ready for the AI era.”
Optro’s latest Risk Intelligence report found that AI governance program maturity is advancing, but unevenly. AI adoption continues to outpace AI governance, with 85 percent of organizations reporting they have integrated AI into their core operations or deployed it across multiple functions, while only a quarter report comprehensive visibility into employee AI use. At the same time, only 34 percent of organizations report their AI governance program is strategic and continuously improving. As these challenges become increasingly prevalent across industries, Optro has released the following product capabilities to help customers turn clarity into action:
- Unified AI Governance: Serves as the essential orchestration layer for AI governance. By bridging the gap between policies & frameworks, your AI tech stack, and human oversight, this capability enables a unified, automated approach. We ensure that AI risks are visible, compliance is streamlined, and governance policies are enforceable across your entire organization.
- Cyber Risk: Vulnerability Risk Monitoring: Provides a clear narrative of how a specific vulnerability affects an organization’s security posture and bottom line. This AI-powered functionality enables customers to understand the true business impact of a vulnerability. Included with IT and Cyber Risk Management (formerly IT Risk Management), it’s a paradigm shift in how organizations defend their digital perimeter.
- Continuous Control Monitoring: With AI-driven recommendations for the controls best suited for automation, and a library of ready-to-use monitor templates, teams can bypass manual setup to start monitoring controls immediately. This capability helps customers reduce manual effort, improve consistency, and gain more timely visibility into control performance. By automating evidence collection and surfacing potential issues earlier, teams can address gaps more efficiently and move toward a more continuous approach to assurance.
-
News10 years ago
SENDQUICK (TALARIAX) INTRODUCES SQOOPE – THE BREAKTHROUGH IN MOBILE MESSAGING
-

 Tech News2 years ago
Tech News2 years agoDenodo Bolsters Executive Team by Hiring Christophe Culine as its Chief Revenue Officer
-

 VAR1 year ago
VAR1 year agoMicrosoft Launches New Surface Copilot+ PCs for Business
-

 Trending6 months ago
Trending6 months agoOPPO A6 Pro 5G Review: Reliable Daily Driver
-

 Tech Interviews2 years ago
Tech Interviews2 years agoNavigating the Cybersecurity Landscape in Hybrid Work Environments
-

 Tech News9 months ago
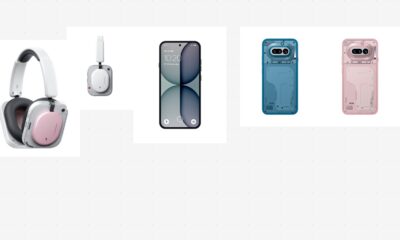
Tech News9 months agoNothing Launches flagship Nothing Phone (3) and Headphone (1) in theme with the Iconic Museum of the Future in Dubai
-

 Automotive2 years ago
Automotive2 years agoAGMC Launches the RIDDARA RD6 High Performance Fully Electric 4×4 Pickup
-

 VAR2 years ago
VAR2 years agoSamsung Galaxy Z Fold6 vs Google Pixel 9 Pro Fold: Clash Of The Folding Phenoms